Blink. That green light on your SOHO router flickers in the dim home office, oblivious to the Russian military code now rewriting its DNS settings.
This isn’t sci-fi. Microsoft’s latest threat intel drops the bomb: Forest Blizzard—a Russian military outfit also known as Storm-2754—has been cracking into vulnerable small office/home office routers since at least August 2025. They’re not just poking around. No, they’re hijacking DNS requests at scale, turning thousands of devices into unwitting beacons for their ops. Over 200 organizations, 5,000 consumer gadgets—impacted, per Microsoft. And that’s before the real fun: adversary-in-the-middle attacks on TLS connections, snagging Outlook web traffic like it’s 1999 dial-up eavesdropping.
How Forest Blizzard Cracks Your Router Open
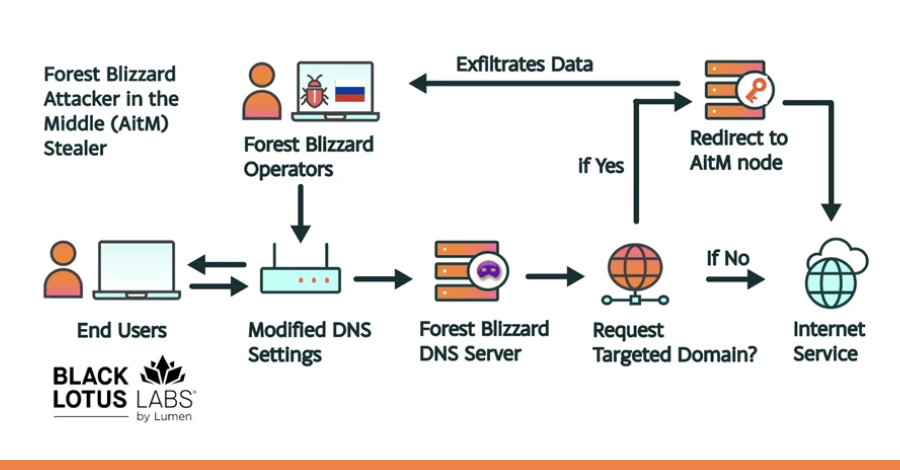
Start simple. These guys target edge devices—your cheap SOHO routers that barely get firmware updates. They slip in via known vulns, no zero-days needed. Once inside, bam: they tweak the DHCP settings. Now every device on your net pings their controlled DNS servers. dnsmasq, that lightweight tool baked into most home routers for DNS forwarding? They’re twisting it into a listener on port 53, slurping queries like a vacuum.
It’s passive gold. DNS logs reveal what sites you’re hitting, who you’re emailing—recon at zero cost. But here’s the kicker: from your compromised home setup, they pivot upstream. Remote worker’s router leads to enterprise clouds. Secure perimeter? Useless if the front door’s wide open.
And Microsoft notes—no hits on their own stuff. Convenient, right? (Though telemetry’s their game, so maybe they’re just not telling.)
Microsoft Threat Intelligence has identified over 200 organizations and 5,000 consumer devices impacted by Forest Blizzard’s malicious DNS infrastructure; telemetry did not indicate compromise of Microsoft-owned assets or services.
Short para punch: Scale matters. This ain’t boutique hacking.
Why Target SOHO? The Unmanaged Backdoor Economy
Think about it. Enterprises lock down servers, but that Netgear from 2018 in Bob’s basement? Forgotten. Hybrid work exploded it—millions of unmanaged edges now bridge home to corp nets. Forest Blizzard knows: low investment, high yield. Compromise one router, watch a neighborhood’s traffic flow.
Historically? Echoes of the 2016 Mirai botnet, where IoT zombies DDoSed the web. But this—state-sponsored, intel-focused—feels colder. My take: we’re seeing the blueprint for the next cyber Cold War. Nation-states won’t brute-force clouds anymore; they’ll burrow into consumer sprawl. Prediction? By 2027, smart fridges and bulbs join the party, DNS-poisoned en masse. Your Nest cam as Putin’s peephole.
Organizations scoff at “home risk.” Wrong. One AiTM’d Outlook session leaks creds, game over. Sectors hit: gov, IT, telecom, energy—Forest’s favorites.
Dense dive: They don’t stop at DNS. Post-hijack, AiTM on TLS. Fake certs intercept Outlook traffic. Microsoft’s seen it—targeted, but scalable. Broader access means they could flip the switch anytime for mass man-in-the-middle. Edge compromise to cloud theft, all proxied through legit-looking routers. Stealthy as hell.
One sentence: Terrifying.
But wait—dnsmasq’s legit, right? Yeah, that’s the beauty. No red flags; it’s your router’s own tool, hijacked.
Can You Spot the Hijack Before It’s Too Late?
Detection’s tricky. Check your router logs for weird DNS IPs. Run nslookup on known sites—does it resolve to oddballs? Microsoft pushes Defender hunts: query for dnsmasq anomalies, port 53 spikes to foreign resolvers.
Mitigate hard. Firmware updates—force ‘em. Swap defaults: custom DNS like 1.1.1.1. Segment networks; VLAN that IoT crap. For orgs, zero-trust home access—verify devices before cloud handoff.
Here’s the thing—Microsoft’s sharing TTPs is gold, but their blog glosses the panic. “No Microsoft impact,” they say, like that absolves the ecosystem. Callout: this exposes hybrid work’s underbelly. We’ve built fortresses around data centers while leaving the drawbridge unmanned.
Wander a sec: Remember SolarWinds? Supply chain pain. This is consumer chain—worse, because it’s everywhere.
The Bigger Shift: From Bots to Intel Farms
Architecturally? DNS hijacking’s old hat for Ruskies, but scaling to AiTM via SOHO? Fresh. It flips the script: attackers hide behind victims’ gear, not their own C2s. Legit IPs, trusted paths—defenders chase ghosts.
Unique angle: Parallels WWII codebreakers at Bletchley—passive intercepts won wars. Forest Blizzard’s building a modern Enigma net, one router at a time. Bold call—this campaign’s testbed for election-season ops. Imagine DNS-flipped traffic during 2028 polls.
Medium para: Users, wake up. That “free” router from your ISP? ticking bomb.
🧬 Related Insights
- Read more: Claude Code Leak Hands Rivals AI’s Secret Sauce
- Read more: Mercor’s 4TB Nightmare: LiteLLM’s Supply Chain Poison Reaches AI Hiring Giant
Frequently Asked Questions
What is SOHO router compromise by Forest Blizzard?
Russian military hackers (Forest Blizzard) exploit vulnerable home/small office routers to hijack DNS, spy on traffic, and enable AiTM attacks on secure connections like Outlook.
How do I check if my router is compromised?
Inspect DNS settings for unknown servers (e.g., via router admin page), monitor logs for dnsmasq oddities on port 53, and test resolutions with tools like dig or nslookup.
Will this affect my enterprise network?
Yes, if remote workers use unmanaged SOHO devices—compromised home routers can proxy attacks into cloud services, bypassing perimeters.