FBI agents hit enter. Poof— a swarm of hacked routers goes dark. Russia’s elite spies, the ones who crashed the DNC and meddled in elections, just lost their digital periscope into American homes and offices.
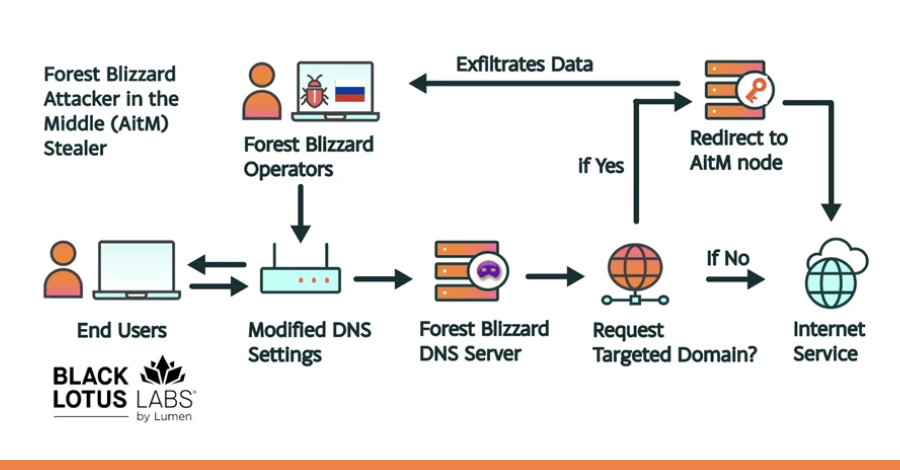
Zoom out. This isn’t some script-kiddie joyride. The Justice Department dropped the hammer Tuesday on APT28— aka Forest Blizzard, Fancy Bear, pick your poison— all tentacles of the GRU. They infected TP-Link and MikroTik SOHO routers, the cheap crap sitting under desks worldwide. Tweaked DHCP and DNS. Boom. Your traffic— emails, logins, cat videos— rerouted through Moscow’s servers.
Adversary-in-the-middle. Fancy term for man-in-the-middle on steroids. They snag passwords, tokens, even encrypted stuff if you— like an idiot— click past those screaming TLS warnings. Worked like a charm on 5,000 consumer devices and 200 orgs, says Microsoft.
Here’s the kicker. They exploited CVE-2023-50224, a hole TP-Link should’ve patched yesterday. But no. Ships vulnerable. Users buy blind. Spies feast.
How’d These Clowns Hijack Your Wi-Fi?
Forest Blizzard— Microsoft’s pet name— slips in via that CVE. Owns the router. Fires up dnsmasq, that legit tool for home networks. Listens on port 53. Your DNS queries? Proxied mostly clean. But for juicy targets? Spoofed straight to their trap servers.
“Forest Blizzard gained access to SOHO devices then altered their default network configurations to use actor-controlled DNS resolvers. This malicious re-configuration resulted in thousands of devices sending their DNS requests to actor-controlled servers.”
Microsoft nailed it. Transparent proxy for most. Spoof for VIPs. Harvest data. Drop malware. Even DoS if they’re feeling petty. Lumen’s Black Lotus Labs calls it FrostArmada— peaked December 2025 with 18,000 IPs from 120 countries. Gov agencies, foreign ministries, email providers. All slurped.
And get this— started August 2025, right after UK sanctions on Russian hacks. Tit for tat? Probably. UK NCSC even coughed up IoCs: VPS banners, router models, domains, IPs. Plus defense tips. Like, update your damn firmware.
Short para: We’re patching history.
But let’s not kid ourselves. This echoes 2016’s Yakity-Sax router hacks by the same crew. FBI disrupted that botnet too. Déjà vu. GRU’s playbook: cheap, scalable, deniable. No zero-days needed. Just lazy admins and EOL gear.
Why Should You Care About Some Router Hack?
Your router’s the castle gate. Compromised? Game over. Military intel, critical infra— FBI says they filtered the haul for gold. Indiscriminate dragnet first, targeted sifting later.
“The GRU has indiscriminately compromised a wide pool of U.S. and global victims and then filtered down impacted users, especially targeting information related to military, government, and critical infrastructure.”
FBI’s words. Chilling. But here’s my hot take, absent from the pressers: this is Cold War 2.0, analog style. Remember Berlin tunnels? US and Brits bugged Soviet lines in ‘55. Soviets knew— let it run for show. GRU’s doing the same: noisy ops to distract from stealthier ones. Bold prediction? Expect quantum-resistant encryption pushes from this. Or more finger-pointing at China.
TP-Link, MikroTik— call ‘em out. Years of vulns. No auto-updates. Corporate negligence fuels nation-states. Hype their ‘secure’ lines? Bull. Fix the basics.
Lumen helped zap the infra. Microsoft too. International high-fives. But 120 countries hit? Leakage everywhere.
One sentence: Complacency kills.
And the timing— post-UK sanctions. Revenge porn for hackers? Authentic Antics targeted MSFT clouds. This? Broader net. FrostArmada scaled fast. 18k IPs peak. Law enforcement played whack-a-mole.
Is Your Dusty Router GRU Bait Right Now?
Probably. Check models: TP-Link vulnerable to that CVE. MikroTik too. Update. Or chuck it. FBI’s advice: segment networks, monitor DNS. NCSC echoes: hunt IoCs.
But users ignore cert warnings. Clickety-click. Spies laugh. AitM thrives on dumb.
Unique angle: this exposes SOHO’s Achilles— home office boom post-COVID left millions exposed. No IT pros. Just vibes. GRU bet right.
Dry humor time. Imagine Putin yelling at underlings: “More routers! Steal grandma’s Netflix queue!” Desperation? Nah. Smart asymmetry. Cost ‘em pennies.
Related ops: Aisuru DDoS botnets down. RedVDS cybercrime smashed. Tycoon 2FA limps on. Pattern— LE winning skirmishes, war grinds.
Deep dive: dnsmasq abuse. Legit for caching, DHCP. Hackers pervert it. Port 53 queries forwarded upstream mostly. Targeted spoofs? Connect to fake sites. Credentials flow.
Microsoft tracked Storm-2754 subgroup. Persistent.
The Bigger Spy Game: What’s Next?
Disrupted? Sure. But GRU rebuilds overnight. History says so. 2024 botnet redux.
Critique the spin: DOJ presser gloats disruption. Reality? They filtered victims post-haul. Data’s out. Siloed? Doubt it.
Prediction: Hybrid ops rise. Routers + AI phishing. Or IoT swarms.
Consumers: Buy enterprise-grade. Or learn Linux.
Orgs: Ditch SOHO for SD-WAN. Monitor anomalous DNS.
Wrapping messy: We’re in it. Patch. Vigil.
🧬 Related Insights
- Read more: TrueConf’s Poisoned Updates Infect Southeast Asian Gov Networks
- Read more: FrostArmada’s Fall: How Cops Crushed Russia’s Router Spy Network Targeting Microsoft Logins
Frequently Asked Questions
What routers are hit by the Russian GRU hack? TP-Link and MikroTik SOHO models, via CVE-2023-50224. Update firmware now— or replace.
How does DNS hijacking steal your data? Hackers reroute queries to their servers, spoof responses for targets, snag creds via AitM even on ‘encrypted’ traffic if you ignore warnings.
Is the FBI’s router disruption permanent? Nope. GRU rebuilds fast— same crew hit before. Stay vigilant; check NCSC IoCs.