Picture this: late-night coffee in a Kyiv apartment, router humming innocently in the corner, while Russian operatives siphon credentials from government emails halfway around the world.
APT28 DNS hijacking. It’s not some sci-fi plot—it’s the new reality of cyber espionage, where everyday SOHO routers become unwitting pawns in a global game of shadows. Russia-linked Forest Blizzard, as Microsoft calls them, kicked this off back in May 2025. Limited at first. Then boom—by December, over 18,000 unique IPs from 120 countries lighting up their command-and-control servers. MikroTik and TP-Link devices, those cheap workhorses in homes and small offices, got exploited en masse.
Here’s the thing. These aren’t fortified enterprise firewalls we’re talking about. No, sir. SOHO gear—small office, home office—sits wide open, forgotten in closets, running ancient firmware. APT28 slipped in, tweaked DNS settings, and voilà: your traffic reroutes through their malicious resolvers. It’s like handing the keys to your digital castle to a fox in the henhouse.
How Did APT28 Pull Off This Router Takeover?
They started simple. Remote admin access on vulnerable boxes. For TP-Link WR841N, it was CVE-2023-50224—an auth bypass that let them yank stored creds with a sneaky HTTP GET. MikroTik routers in Ukraine? Targeted harder, funneled to secondary clusters for interactive ops.
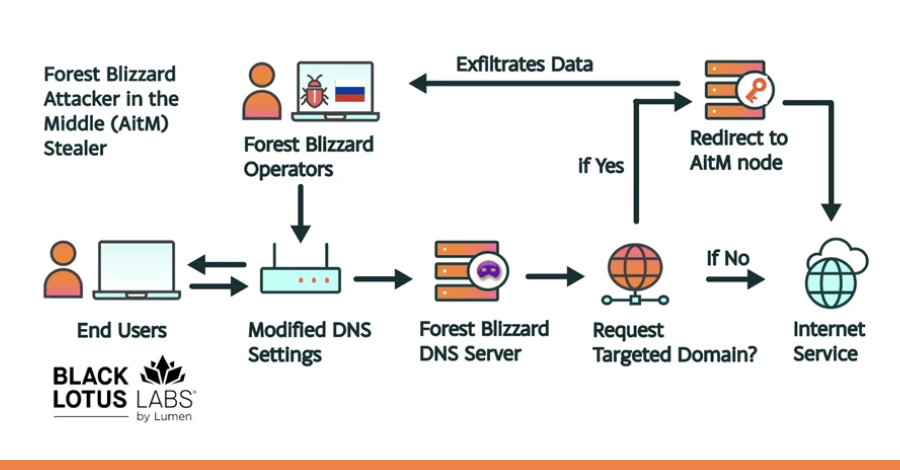
Once inside, DNS gets poisoned. Your router now queries actor-controlled servers. You fire up Outlook on the web? Boom—redirected to an attacker-in-the-middle node. No pop-ups. No warnings. Just silent credential theft. OAuth tokens, passwords, all harvested passively.
“Their technique modified DNS settings on compromised routers to hijack local network traffic to capture and exfiltrate authentication credentials,” Black Lotus Labs reported.
Black Lotus Labs dubbed it FrostArmada. Microsoft pinned it on APT28’s Storm-2754 subgroup. And get this—the U.K.’s NCSC says it’s opportunistic: cast a wide net, then triage for high-value intel targets like foreign ministries in North Africa or Southeast Asia.
But wait. Energy here—think of it like the old Cold War listening posts, but supercharged. Back then, spies bugged embassy phones. Now? They own the pipes. Routers upstream of enterprises, less monitored, perfect pivot points into bigger fish.
Why SOHO Routers? The Perfect Spy Platform
Scale. Stealth. Persistence.
Nation-states crave this. DNS hijacking gives passive recon at massive volume. Microsoft nailed it:
“For nation-state actors like Forest Blizzard, DNS hijacking enables persistent, passive visibility and reconnaissance at scale.”
Your enterprise VPN might be ironclad, but that coffee shop Wi-Fi or remote worker’s TP-Link? Wide open. APT28 hit 200+ orgs, 5,000 consumer devices. Governments in Central America, Europe—law enforcement, cloud providers. Even AiTM on TLS connections, first time at this scale for them.
And the disruption? U.S. DOJ, FBI, international partners took down the infra. Good news. But here’s my unique take, the one you won’t find in the original reports: this is the blueprint for AI-augmented swarms. Imagine bots scanning billions of routers 24/7, auto-exploiting vulns, self-healing networks. We’re not there yet—but FrostArmada feels like the Wright brothers’ flight in cyber terms. A fundamental shift, where edge devices form digital militias.
Skeptical? Sure, corporate spin from Microsoft calls it novel, but it’s evolution, not revolution. They’ve done router ops before; this just scales it globally. Still, wonder at the audacity—18,000 nodes, invisible exfil. It’s poetry in malice.
Look, vendors like TP-Link patched that CVE months ago. But millions lag. Firmware updates? Manual drudgery. And MikroTik? Notorious for insecure defaults.
Is Your Router Next in APT28’s Sights?
Probably. If it’s SOHO, unpatched, exposed—yes.
They filtered targets dynamically: DNS logs reveal users, then AiTM narrows to intel gold. African gov orgs hit hard, Outlook phishing proxies spotted. Opportunistic, but laser-focused on espionage.
Prediction time—bold one: by 2027, we’ll see AI models predicting vuln chains, auto-deploying AitM. Routers as the new frontier in platform wars. AI isn’t just chatbots; it’s the OS for cyber conflict.
Protect yourself. Change default creds. Enable auto-updates (if they exist). Use DNS like Quad9 or Cloudflare’s 1.1.1.1—malware struggles there. VPNs help, but edge compromise laughs at them.
This campaign’s down, but APT28? They’re eternal. Like digital cockroaches.
And the human cost? Stolen creds lead to pivots—broader compromises. Think SolarWinds, but quieter, router-borne.
Why Does Router Hijacking Matter for the Future of Security?
Because it’s asymmetric. States vs. individuals—or small biz. One vuln, global reach.
Historical parallel: Trojan Horse, but wireless. Greeks hid in wood; Russians in firmware.
Energy builds—fix this, and we harden the net’s capillaries. Ignore? Floodgates open for worse.
Microsoft disrupted some, but actors adapt. Storm-2754 already eyeing Ukraine routers specifically.
Vivid analogy: routers as neighborhood watchmen, now turncoats whispering secrets.
🧬 Related Insights
- Read more: Cloud Phones Let Crooks Rent Victim Mimics for Pennies, Dodging Bank Defenses
- Read more: NoVoice Malware’s Rampage: 2.3 Million Android Phones Rooted via Google Play
Frequently Asked Questions
What is APT28 and FrostArmada?
APT28 (Forest Blizzard) is a Russian state-linked hacker group behind FrostArmada, a DNS hijacking campaign using compromised SOHO routers for credential theft since May 2025.
How to secure my home router from DNS hijacking?
Update firmware immediately, change default passwords, use secure DNS resolvers like 1.1.1.1, and monitor for unusual traffic.
Does APT28 DNS hijacking affect consumers or just governments?
It hit 5,000 consumer devices alongside 200 orgs—anyone with vulnerable MikroTik or TP-Link routers could be pivoting to bigger targets.