Ever wonder if that blinking light on your router is winking back at the Kremlin?
Yeah, me neither—until now. The US Department of Justice and FBI just dismantled a sprawling DNS hijacking network run by Russia’s notorious APT28 hackers, yanking control from over 23 states’ worth of compromised routers. It’s like pulling the plug on a digital vampire mid-feast, credentials dripping from its fangs.
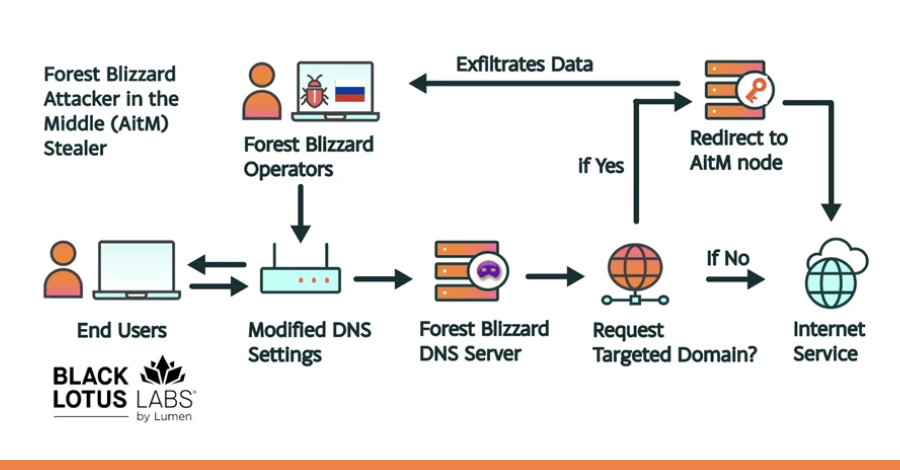
This isn’t some script-kiddie prank. APT28—tied straight to Russia’s GRU Military Unit 26165—has been prowling since 2024, zeroing in on vulnerable SOHO routers, especially TP-Link models. They slip in through unpatched holes, twist DNS settings to reroute traffic through their servers, and harvest login creds from high-value targets. Intelligence goldmine, right there in your living room.
Operation Masquerade: The Digital Exorcism
Picture this: FBI agents in Boston, court warrant in hand, crafting surgical code strikes. Not bombs—commands. Sent to infected routers across the US, these zap APT28’s malicious DNS resolvers, reset everything to ISP-legit settings, and lock the backdoor. Tested rigorously on TP-Link gear, no collateral damage to your Netflix queue or grandma’s cat videos.
And get this—they made it reversible. Hit that hardware reset button, or log in and factory-default it. Users get notified via ISPs. It’s cyber surgery with a polite follow-up note.
“Russian military intelligence once again hijacked Americans’ hardware to commandeer critical data. In the face of continued aggression by our nation-state adversaries, the US government will respond just as aggressively.” — David Metcalf, US Attorney for the Eastern District of Pennsylvania
Boom. That’s the fire. Metcalf’s words hit like a Cold War mic drop.
The op pulled in heavy hitters: Philadelphia FBI, National Security Cyber Division, Lumen’s Black Lotus Labs, Microsoft Threat Intelligence, even MIT Lincoln Lab. Global sync too—UK’s NCSC chimed in same day.
But here’s my unique spin, the insight you’re not reading elsewhere: This echoes the 1983 Able Archer crisis, where NATO exercises spooked the Soviets into near-nuclear panic. Back then, misread signals nearly torched the world. Today? Router hijacks are the new false flags—subtle, persistent probes blurring espionage and accident. Except now, we’re not just watching stars for missiles; we’re scripting router rebellions. Bold prediction: By 2026, AI guardians in every firmware will auto-detect and nuke these intrusions, turning consumer gear into self-healing sentinels. APT28? They’ll be chasing ghosts.
Energy surges here. Imagine routers as nomadic tribes on the internet steppe—APT28 as steppe wolves, herding them into ambushes. FBI’s Masquerade? The cavalry with lassos of code.
Why APT28 Loves Your Dusty TP-Link
SOHO routers. Small office, home office—those cheap workhorses powering startups and family Wi-Fi alike. Unpatched? Sitting ducks. APT28 exploits known vulns (think CVE-ridden firmware), no zero-days needed. Just patience and persistence.
They don’t blast in. Nah—quiet redirection. Your browser asks for bank.com? Router sneaks it to fake DNS, logs your creds as you type. Victims? Orgs of intel value—think defense contractors, journos, activists.
Scale? Massive. US takedown hit the American slice; global remnants lurk. UK NCSC, Microsoft—all sounding alarms.
“GRU actors compromised routers in the US and around the world, hijacking them to conduct espionage. Given the scale of this threat, sounding the alarm wasn’t enough.” — Brett Leatherman, FBI Cyber Division Assistant Director
Leatherman nails it. Alerts are whispers; this was a shout with fists.
Is Your Router Next on Putin’s List?
Look—don’t panic-surf Amazon yet. But check. Outdated firmware? End-of-life model? You’re rolling dice in a casino run by GRU.
DoJ’s playbook: Swap old routers. Patch firmware from official sites only. Scrub DNS to ISP defaults (8.8.8.8? Fine, but verify). Kill remote admin. Follow TP-Link’s hardening guide—or whoever your brand.
FBI wants reports via IC3 or local offices. We’re all in this net, folks.
And the wonder? This takedown previews a fortified future. Routers evolving—mesh networks with quantum-resistant encryption, AI sniffing anomalies like bloodhounds. No more lone wolves; packs of smart defenses.
Skeptical? Sure, corporate router makers hype ‘secure by design’ post-breach. But Masquerade proves governments won’t wait— they’ll rewrite the rules themselves.
Pace picks up. Russia’s grinding cyber war—SolarWinds, NotPetya—meets US counterpunch. Not flawless; overseas routers untouched. But momentum shifts.
Why Does This Matter for the AI Era?
Routers as chokepoints. AI’s gobbling data—your edge devices feed it. Hijacked DNS? Poisons the well, skews training sets, spies on inferences. Futurist alert: Secure pipes or bust.
Unique parallel—think Enigma machines in WWII. Nazis’ rotor codes cracked by Poles, Brits. Today, DNS as the new rotor; FBI’s the codebreakers. Prediction: Expect ‘Masquerade 2.0’ with ML models predicting hacks pre-strike.
Dense dive: APT28’s playbook—low and slow. No ransomware flash. Espionage demands stealth. Counter? Proactive resets like this. But scale globally? Needs treaties, shared threat intel. US led; allies follow?
One sentence: Thrilling win.
Then sprawl: Agencies collabed smoothly—public-private mashup that’d make sci-fi jealous. Lumen spotting patterns, Microsoft decoding C2, MIT modeling firmware. Result? Hackers blind, routers freed. Yet, human element lingers—users must act. Apathy’s the real vuln.
Medium bit. Russia’s GRU won’t quit. Persistent threat, per Eisenberg.
🧬 Related Insights
- Read more: Grafana’s AI Feature Was One Sneaky Web Page Away from Spilling Secrets
- Read more: Google’s Developer Verification Plan Buries Android’s Open Roots
Frequently Asked Questions
What is APT28 and why are they targeting routers?
APT28 (aka Fancy Bear, GRU Unit 26165) is Russia’s military cyber arm, hitting routers for stealthy credential theft via DNS redirects. Cheap, effective espionage.
How do I check if my router was hit by this DNS hijacking?
Log in, inspect DNS settings (should match ISP), run firmware updates, scan for odd traffic. Use tools like routerlogs or FBI IC3 report.
Will the FBI’s Operation Masquerade protect routers worldwide?
No—just US portion. Global users: Patch now, disable remote access, consider upgrades. It’s a blueprint, not a blanket.