You’re a defense contractor in Virginia, crunching numbers on the next fighter jet sim. Suddenly, Beijing’s playbook — every aerospace tweak, every missile trajectory — hits the dark web. That’s the nightmare unfolding if this 10 petabytes stolen from China’s National Supercomputing Center claim holds water.
Forget the headlines chasing hacker brags. Real people — scientists grinding grants, engineers chasing contracts — now wonder if their edge just evaporated. I’ve covered Valley leaks for two decades; this one’s scale screams trouble for anyone betting on tech supremacy.
Who Actually Got Robbed Here?
China’s NSCC in Tianjin isn’t some backwater server farm. It’s the nerve center for 6,000 outfits — think AVIC jets, COMAC airliners, even National University of Defense Technology war games. Hackers under ‘FlamingChina’ dropped samples on Telegram back in February: secret-labeled files, bomb renders, fusion sims. Aerospace. Bioinformatics. Weapons.
Analysts poked at the leaks. Authentic, they say. And the price tag? Samples for thousands in crypto; full 10PB haul runs hundreds of grand.
The exposed materials include files labeled ‘secret’ in Chinese, along with engineering documentation, simulation results, and rendered models tied to weapons systems such as bombs and missiles, according to analysts who reviewed portions of the leak.
That’s straight from the reports. Chilling, right? Not hype — cold cash for state secrets.
But here’s my take, the one nobody’s yelling yet: this mirrors the SolarWinds mess in 2020, only flipped. Back then, Russia snuck into U.S. pipes for years. Now? China’s centralized supercomputing bet — pour everything into one fat target — bites back hard. We’ve warned about single points of failure since the ’90s mainframe days. Beijing ignored it. Bold prediction: expect copycats hitting other national labs worldwide. Decentralize or die.
Is This Hack Even Real?
CNN couldn’t verify — shocker. But cyber experts nodded at samples: matches NSCC guts perfectly. Attacker? Compromised VPN, then botnet drip-feed over six months. No fireworks, just patient plumbing exploits. Sneaky. Effective.
Stealing 10PB? That’s 10 million gigabytes. Exabytes lurk in clouds, sure, but undetected? Requires god-tier stealth, monster bandwidth, and nerves. Individuals? Nah. Nation-state vibes, or well-funded crew. Processing it? Only governments crunch that haystack for needles.
Look, China’s poured billions into firewalls — Great Cannon, anyone? — yet here we are. Systemic rot. VPN slips aren’t ‘advanced persistent threats’; they’re lazy admin 101. Who’s making money? Hackers, flipping data to rivals. Iran? Russia? Us? Follow the crypto.
Short para for punch: Weakness exposed.
And it cascades. That AVIC doc on hypersonic tweaks? Lands in Lockheed hands — boom, U.S. bids tighten. Your tax dollars fund catch-up games now. Everyday Joe? Cheaper jets maybe, but riskier skies if terrorists snag fusion tricks.
Why Does NSCC Matter to You?
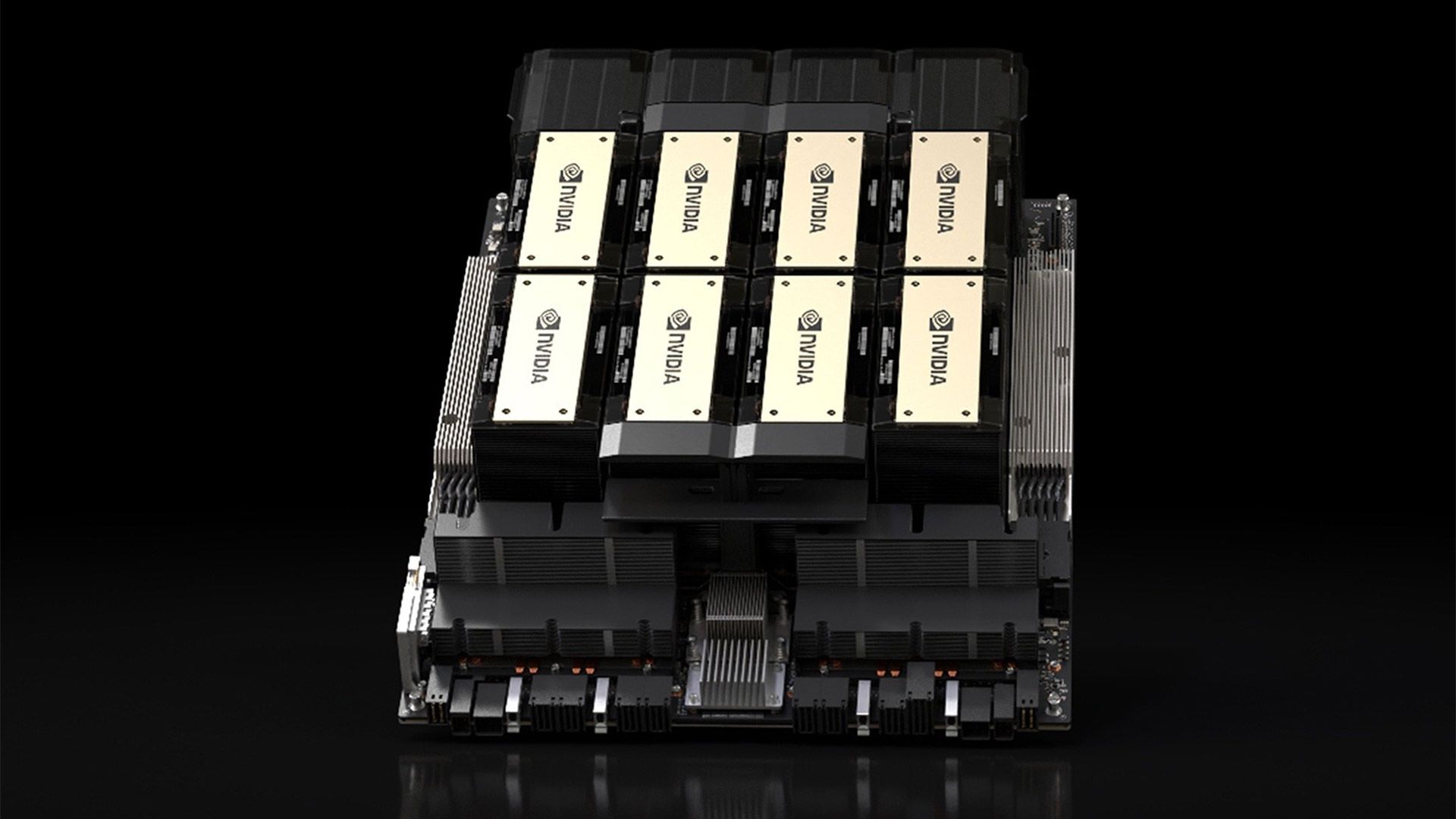
Supercomputing isn’t abstract. Powers drug discovery (bioinformatics leaks), climate models, nukes. NSCC ranks top-tier globally — Tianhe whatever, exascale dreams. Breach this, you gut R&D pipelines.
I’ve grilled execs post-Snowden: ‘How secure?’ Crickets, then platitudes. China? Same spin — ‘isolated incident’ incoming, bet on it. But 6,000 clients? That’s every prof, every firm leaning on state juice.
Cynical me asks: profit angle? Hackers cash in quick. Buyers? Intel agencies padding dossiers they half-knew already. Real winners? Decentralized cloud players like AWS, whispering ‘told you so’ to spooked clients.
Six sentences here, dense: First, exfiltrate smart — no bulk dumps. Second, botnets mask traffic. Third, six months buys complacency. Fourth, VPN holes persist ‘cause patching’s boring. Fifth, labels like ‘secret’ scream value. Sixth, global ripple: alliances shift as data democratizes darkly.
Fragment. Terrifying.
What Happens Next?
If real — and signs point yes — Beijing clamps. Purges. Blame foreigners. But fixes? Nah, politics first. Meanwhile, samples circulate. Full dump? Dark markets explode.
Unique spin: parallels Enron’s off-books games, but digital. China hid supercomputing scale; now it’s Pandora’s exabyte. Prediction: U.S. Congress hearings, export bans tighten. Valley firms? Stock dips on China exposure.
Real people hit: researchers pivot, fearing tainted sims. Investors bail on dual-use tech. You? Safer apps if weapons R&D stalls — silver lining?
**
🧬 Related Insights
- Read more: Ditch Amazon’s Lockdown: Convert EPUB to Kindle Before It’s Too Late
- Read more: Inference Scaling: Why It’s Silently Crushing LLM Training Limits
Frequently Asked Questions**
What is China’s National Supercomputing Center?
Tianjin’s NSCC powers 6,000 entities with elite HPC for defense, aero, science — now allegedly cracked wide open.
Is the 10 petabytes NSCC data breach confirmed?
Not officially, but expert-vetted samples look legit; scale suggests state-level play.
How was the China supercomputing hack pulled off?
VPN compromise, botnet exfil over months — basic exploits, epic patience.