Picture this: you’re typing your Microsoft 365 password, coffee steaming, deadline looming. Unseen, your router—yeah, that TP-Link or MikroTik gathering dust—reroutes your login straight to a Russian proxy. Credentials snatched. OAuth tokens swiped. Welcome to FrostArmada, the slick DNS hijack op that peaked at 18,000 infected devices worldwide.
And just like that—bam—it’s over. An international posse of cops, Microsoft, and Lumen’s Black Lotus Labs yanked the plug on the whole shebang. FBI, DOJ, Polish gov in the mix. Malicious VPS servers? Dark. Botnet? Dismantled. But rewind: how’d Russia’s APT28—Fancy Bear, Forest Blizzard, those GRU wolves—pull this off without a whisper?
What the Hell Was FrostArmada?
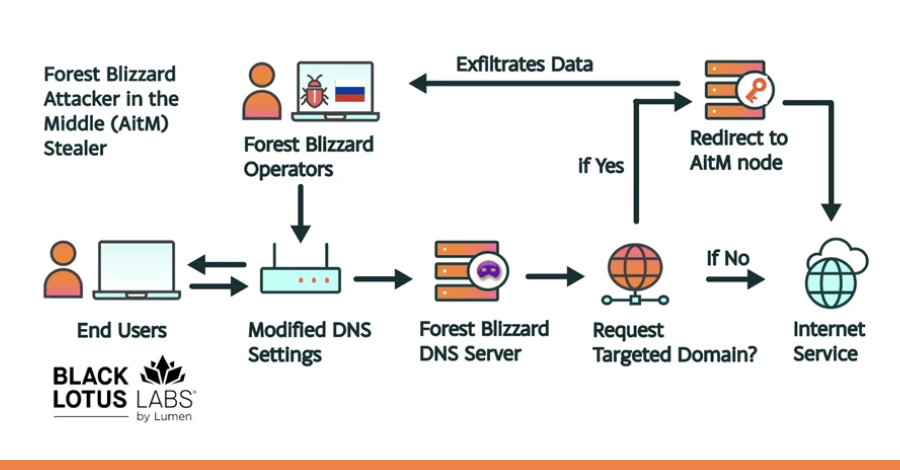
Hackers zeroed in on SOHO routers, the workhorses of small offices and homes. MikroTik, TP-Link, even some crusty Fortinets and Nethesis firewalls. Compromise ‘em via internet exposure—easy pickings. Then, DNS settings flipped to point at attacker VPSes masquerading as resolvers.
Traffic to Microsoft auth domains? Intercepted. DHCP pushes the bad DNS to every gadget on your network. Boom—adversary-in-the-middle (AitM) proxy awaits. Victims see a TLS cert warning, shrug it off (who reads those?), and hand over the keys to their digital kingdom.
“The actor essentially ran a proxy service as the AitM that the end user was directed to via DNS,” Lumen’s Black Lotus Labs researchers explain. “The only sign of this attack would be a pop-up warning about connecting to an untrusted source because of the ‘break and inspect’ configuration.”
That’s the genius— or nightmare. Proxies snag unencrypted creds mid-flight, relay to real services. Tokens harvested. Sessions hijacked. And it spiked post a UK NCSC report in August 2025 outing Forest Blizzard’s Microsoft token grab.
Targets? Governments, law enforcement, IT crews, hosting firms, self-hosted server ops. North Africa gov servers (non-Microsoft), Central America, Southeast Asia. Even a European national ID platform got sniffed.
One paragraph wonder: Two clusters ran the show—‘Expansion team’ bloating the botnet, ops crew harvesting creds.
How Did They Sneak Past Your Defenses?
DNS hijacking’s old-school elegant, like rewiring the Yellow Pages to funnel calls to mobsters. But FrostArmada scaled it. Devices phone home post-compromise, snag DNS tweaks, propagate via DHCP. Query Outlook web? Fake IP. Spoofed responses in spots, per Microsoft.
Browser or desktop app—didn’t matter. Opportunistic, they say: infect en masse, filter for gold. 120 countries, peak December 2025. Black Lotus Labs mapped it with Microsoft, traced victims.
Here’s the IOC table they dropped—check your logs:
| IP address | First Seen | Last Seen |
|---|---|---|
| 64.120.31[.]96 | May 19, 2025 | March 31, 2026 |
| 79.141.160[.]78 | July 19, 2025 | March 31, 2026 |
| 23.106.120[.]119 | July 19, 2025 | March 31, 2026 |
| 79.141.173[.]211 | July 19, 2025 | March 31, 2026 |
| 185.117.89[.]32 | September 9, 2025 |
Short and sharp: Patch. Now.
But look—my hot take, absent from the pressers. This ain’t just cybercrime; it’s the Stuxnet of suburbia. Remember Stuxnet’s air-gapped Iranian nukes? FrostArmada democratizes that precision for every SMB. Bold prediction: expect ‘FrostArmada 2.0’ from peer adversaries—China’s APT41, Iran’s pack—tuning routers into credential farms. Why? Platform shift: routers as the new IoT battlefield, where nation-states build shadow nets overnight. Wonder at the tech—DNS, DHCP, AitM proxies dancing like quantum bits—but dread the cascade if unpatched fleets linger.
Could Your Router Be the Next Victim?
SOHO gear’s the soft underbelly. Exposed management interfaces, default creds, forgotten firmware. APT28 exploited that, but anyone’s game. Governments in Africa saw DNS intercepts on their own servers—no Microsoft needed. Law enforcement? IT providers? If you’re self-hosting email or auth, you’re meat.
Microsoft’s report flags M365 subdomains, Outlook web. But it spilled wider—on-prem servers, identity platforms. Opportunistic? Sure, till it nets a diplomat’s token.
Vivid bit: Imagine your router as a Trojan horse in ancient walls—quietly redirecting scouts to the enemy camp. That’s FrostArmada. Takedown’s a win, yet echoes Cold War tradecraft: GRU’s 85th GTsSS unit 26165, same crew behind election hacks, Olympics doping dumps. Persistent. Ruthless.
Dense dive: Response was textbook—private threat intel (BLL) meets public muscle (FBI/DOJ/Poland). Infra nuked. Victims alerted? Microsoft says yes. But cleanup? Routers need resets, DNS audits, DHCP scrutiny. Enterprises: segment networks. Homes: firmware up, no remote admin. And that cert warning? Heed it, or pay.
Why Does This Takedown Signal Bigger Storms?
Energy here—it’s a futurist’s thrill mixed with chills. Cyber’s evolving from brute ransomware to surgical intel ops. FrostArmada proves routers aren’t plumbing; they’re chokepoints in the AI-era platform shift (wait, hear me: AI agents will authenticate everywhere—steal those tokens, own the swarm). Takedown disrupts, doesn’t deter. GRU rebuilds botnets like clockwork.
Skepticism on PR spin: Microsoft’s all “we teamed up,” but they were prime targets—own that exposure. Lumen’s clusters insight? Gold, but why no full IOC dump? Partial list screams ‘tip of iceberg.’ Still, props to the smash—18K devices freed, creds potentially saved from Moscow vaults.
Punchy close: Check your gear. Change DNS manually if paranoid—1.1.1.1 or 8.8.8.8. Wonder wanes when your inbox is the prize.
🧬 Related Insights
- Read more: Meta Ghosts Mercor After Breach Spills AI Training Secrets
- Read more: TeamPCP’s Supply Chain Onslaught Hits Databricks, Splits Ransomware Into Two Deadly Tracks
Frequently Asked Questions
What is FrostArmada?
FrostArmada’s APT28’s (Russian GRU) campaign hijacking SOHO routers via DNS changes to steal Microsoft 365 logins and tokens from 18K devices in 120 countries.
How to protect against router DNS hijacking?
Update firmware, disable remote admin, monitor DHCP/DNS settings, heed TLS warnings, use known-good resolvers like Quad9.
Is APT28 still active after FrostArmada takedown?
Disrupted, not destroyed—expect pivots; watch for similar ops from Forest Blizzard aliases.