What if your million-dollar firewall is handing hackers the keys to your data vault—on purpose?
I’ve been kicking tires on enterprise security gear since the dial-up days, and this one’s a doozy. During a routine pentest, some sharp-eyed assessor finds an open TCP port staring out at the wild internet. Firewall? Sure, a beefy Palo Alto with App-ID cranked on. But data exfiltration? Piece of cake—or so it seems. Pump a tarball through netcat, and bam—cut off at 5KB. Every time.
Here’s the quote that nails it from the discovery:
“The main issue with this technique is that enough packets must be sent over the wire to perform a good classification. So, the traffic is always allowed first and, if something bad is detected, remaining packets are blocked.”
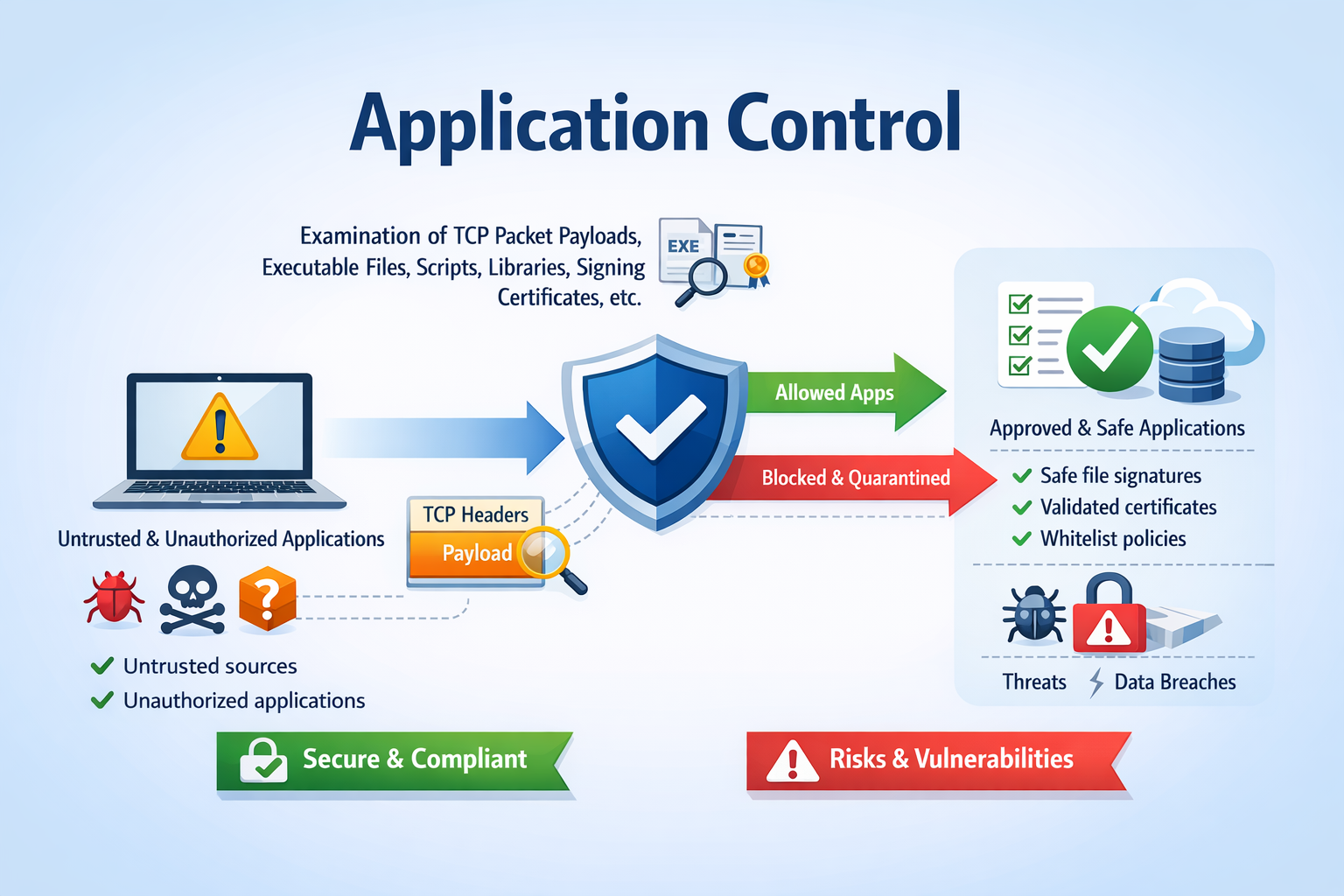
Spot on. App-ID—Palo Alto’s crown jewel, echoed in Checkpoint’s App Control or Fortinet’s version—sniffs traffic like a bloodhound. Ports? Who cares. It peers into payloads, TLS handshakes, even encrypted streams, tagging ‘Facebook’ or ‘Dropbox’ before slamming the door. But that sniffing takes time. And data. Roughly 5-10KB to get confident.
Why Next-Gen Firewalls Let Hackers Start the Party
Think about it. Your firewall’s playing catch-up. First packets? Harmless handshakes, generic TCP blips—“unknown app,” so they pass. Bad guy sends more? Now it patterns: oh, that’s data exfiltration, block. Too late. Those initial kilobytes are gone. And in a breach, exfil’s the nightmare—backups fix encryption, but stolen PII dancing on dark web servers? Kiss it goodbye.
The netadmin shrugs: “App-ID’s enabled.” Yeah, and? This isn’t brand-specific; any deep-packet inspector with a learning curve has this blind spot. Remember the early 2000s, when stateful firewalls got cocky? Attackers tunneled HTTP over port 443 to sneak by. History rhymes—buzzword firewalls promise the moon, but physics (or TCP/IP) bites back.
Short version: They’re reactive. Always.
The Chunked Exfil Hack That Slips Right Through
So, bypass time. Attacker side: netcat in a loop, snagging 3KB chunks with a 5-second timeout. Firewall drops packets mid-stream? No sweat—connection lingers, next chunk fires.
Victim side? Python script splits your juicy data.zip into bitesize pieces—3072 bytes max. Send, retry on fail, repeat. For a 359KB file? 117 chunks, all greenlit because none scream “exfil.” Slow as molasses, sure. But stealthy. No bandwidth spike to alert your SIEM.
Hashes match post-reassembly. Boom—exfiltrated. Proof-of-concept scales to megs; imagine nation-states chunking terabytes over weeks.
And get this—my unique twist: This reeks of Stuxnet-era tradecraft. Remember how they air-gapped Iranian nukes but exfiled via USB then C2? Chunking’s the network equivalent. Low-and-slow persistence beats flashy zero-days every time. Vendors hype ML-driven detection? Please. It’s just delayed port-knocking with payloads.
Is Your Firewall’s App-ID Actually Useless?
Not useless. Damn good at blocking Facebook at work, or Dropbox syncs. But data exfil? When attackers control the pace, you’re toast. Tune timeouts tighter? Legit apps suffer—Zoom calls drop, devs rage. Whitelist every port? Back to 1990s stone age.
Palo Alto folks might counter: “Enable strict profiles, anomaly detection.” Fair. But in practice? Admins loosen rules for “business needs.” That open port? Probably some legacy app. And PR spin incoming: “App-ID evolves with threats.” Sure, until the next blog post like this drops.
One-paragraph rant: Firewalls make bank on fear—application control bypass sells upgrades. Who profits? Palo Alto’s stock (up 20% last quarter). You? Chasing ghosts while hackers chunk away.
Real-World Fallout: Who Gets Hit Hardest
Financials. Healthcare. Any org hoarding CCs or PII. Backups? Great for ransomware. Useless here. Detection? Blue teams watch for beacons, not dribbles. MITRE ATT&CK calls this T1048—exfil over C2. Add chunking, and it’s T1048.003 on steroids.
Prediction: Red teams adopt this yesterday. Pentest reports explode with “App-ID bypassed via micro-chunking.” Vendors scramble patches—maybe ML on transfer patterns. But attackers pivot: ICMP chunks? DNS tunneling 2.0?
Cynical truth—we’ve circle-jerked port/protocol wars for decades. Apps win until they don’t.
Patching the Chunk—Or Just Buy More Hype?
Short-term: Port scans. Lock ‘em down. App-ID? Pair with DLP endpoints—chunk all you want, agents snitch.
Long-term? Zero trust networks. No east-west chatter. But that’s cultural shift, not checkbox.
Here’s the thing—don’t blame the tool. Blame policy. That open port? Symptom.
🧬 Related Insights
- Read more: Storm Infostealer: Hackers Now Decrypt Your Passwords on Their Servers
- Read more:
Frequently Asked Questions
What is application control bypass for data exfiltration?
It’s a technique where attackers split files into tiny chunks (under 5KB) to evade next-gen firewalls’ App-ID, which needs more data to classify and block suspicious traffic.
How does App-ID fail at stopping data exfiltration?
App-ID allows initial packets for analysis—hackers exploit this by sending micro-chunks, restarting connections before classification kicks in fully.
Can I prevent chunked data exfiltration on Palo Alto firewalls?
Tighten timeouts, enable anomaly detection, run endpoint DLP, and audit open ports religiously—but no silver bullet exists yet.