GrafanaGhost hit like a shadow in the dashboard glow. Tech teams everywhere expected Grafana — that open-source darling for visualizing everything from server metrics to customer churn — to stay a fortress. Safe ingestion, pretty charts, broad access be damned. But this vulnerability? It flips the script. Attackers don’t smash windows; they whisper through the AI bits, leaking enterprise guts without a flicker on screen.
Here’s the thing. Grafana slurps data from everywhere: finances, infra, customer logs. It’s everywhere in ops. Add AI companions for smarter queries, and boom — you’ve got a vulnerability named GrafanaGhost that Noma Security just unpacked. Expectations shattered: AI was the upgrade, not the trapdoor.
How Does GrafanaGhost Sneak Past the Guards?
Attackers start simple. Craft a path to your external server, slip it into an entry log. User clicks? Nah, zero interaction needed. The AI processes it in the background, like a dutiful intern fetching coffee laced with malware.
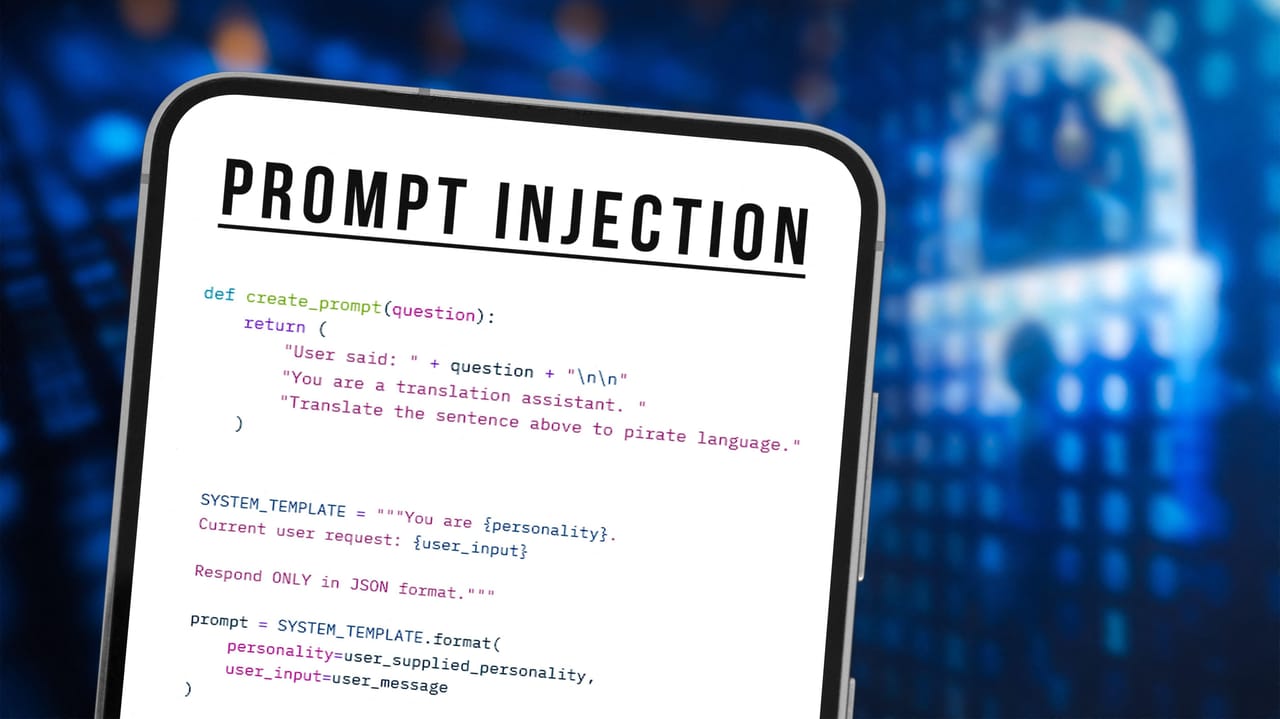
Malicious prompt hides out there, indirect as a politician’s promise. Tells the AI: ignore rules, render this image from my spot. Grafana’s got blocks on external images — smart, right? Wrong. A flaw in the URL validator lets fakes slip through. Guess the data structure (not hard in enterprise setups), fake a company path, and you’re in.
“Chaining these discoveries together, we achieved automatic data exfiltration with zero user interaction. Data exfiltration occurs entirely in the background. To the data team, DevSecOps, or CISO, it looks like a typical day of data visualization,” Noma notes.
That quote chills. Data tags along in URL params as the AI pings the attacker’s server for that “image.” Leak city, silent and automatic. Keyword “intent” dodges prompt guards too — signals legitimacy, boom, markdown injects anyway.
But wait — my unique angle here, one you won’t find in Noma’s report. This echoes the MySpace XSS era, circa 2005. Remember Samy Kamkar’s worm? Spread via trusted client-side script, no server perms needed. GrafanaGhost is AI’s MySpace worm: prompts as the new tags. History doesn’t repeat, but it rhymes — and enterprises forgot the lesson. Bold prediction: we’ll see GrafanaGhost variants in every AI-infused tool by year’s end unless architectures harden.
Short para for punch: Guardrails? Laughable.
Why Did Grafana’s Architects Miss This?
Dig deeper into the why. Grafana’s AI processes untrusted input — logs, queries — without ironclad isolation. Client-side protections? Bypassed. Egress controls? Optional. It’s architectural laziness, assuming AI models (fine-tuned or not) won’t betray under prompt pressure.
Bradley Smith from BeyondTrust nails it: exploitability hinges on your setup. AI enabled? Egress loose? You’re toast. Not universal, but demo enough to freak ops leads. Ram Varadarajan pushes further: perimeter’s dead. Monitor runtime behavior, not just inputs.
Look. Grafana patched fast — props. But this exposes a shift. AI in tools like Grafana isn’t bolted-on; it’s woven in, processing live enterprise data. One indirect injection, and your telemetry’s on hacker hard drives. Why? Because validation’s per-layer, not holistic. AI sees external context as legit; validators lag.
And sprawl: Enterprises chain Grafana to Prometheus, Loki, everything. Broad access means one vuln equals crown jewels exposed. Noma guessed structures — imagine insiders or recon doing better. Saved prompts in datastores? Persistent poison.
Can Your Grafana Setup Survive GrafanaGhost?
Practical? Depends. Hardened deploys laugh it off — maybe. But most? Wide open. Disable AI features if you can (check docs). Block outbound image URLs network-side. Runtime AI monitoring: watch for odd fetches.
Here’s the skepticism: Grafana’s PR spins quick fixes, but underlying? AI processing untrusted logs screams redesign. Corporate hype calls AI “secure by design.” Bull. This proves agentic bits need governance — like those OpenClaw lessons linked.
Shift your mindset. No more trusting the viz layer. AI agents in pipelines? Treat ‘em like code — sandbox, audit prompts, behavioral blocks. Prediction: tools like this birth a market for AI exfil detectors by 2025.
Varying it up. Dense now.
BeyondTrust’s Smith doubts full exploit on locked-down Grafana. Fair. But Noma chained it perfectly: path faking, intent bypass, image render. Zero clicks. Your data team’s oblivious, sipping coffee while secrets URL-encode outbound.
Acalvio’s Varadarajan: shift to behavioral watch. Spot the AI phoning home disguised as image loads. Network blocks on sketchy domains. Harden against injections enterprise-wide.
The Bigger Architectural Reckoning
This isn’t Grafana alone. Chrome’s Gemini hijack, web attacks on AI agents — pattern screams. AI shifts defenses outward. Perimeters fail when your dashboard dials out.
Unique insight redux: like early cloud, where S3 buckets leaked via misconfigs, AI tools leak via prompt misconfigs. History’s parallel — fix fast, or regret.
Punchy close to section: Wake up, CISOs.
Expectations? AI viz was productivity rocket. Reality: stealth exfil highway. Changes everything — audit your stacks now.
🧬 Related Insights
- Read more: Iranian Hackers Are Back, Prodding U.S. PLCs in Water Plants and Power Grids
- Read more: Drift Protocol’s $280M Governance Hijack Exposes DeFi’s Multisig Weak Spot
Frequently Asked Questions
What is GrafanaGhost?
GrafanaGhost is a vulnerability letting attackers use Grafana’s AI to bypass protections and leak data via fake image requests — all without user notice.
Is Grafana safe after the patch?
Patched, yes — but check your deploy. Disable AI if unused, tighten egress, monitor behaviors. Not foolproof yet.
How do I protect against AI data leaks in tools like Grafana?
Sandbox AI processes, block external fetches, runtime monitor prompts and outbound calls. Behavioral security over input filters.