Mythos breaks them all.
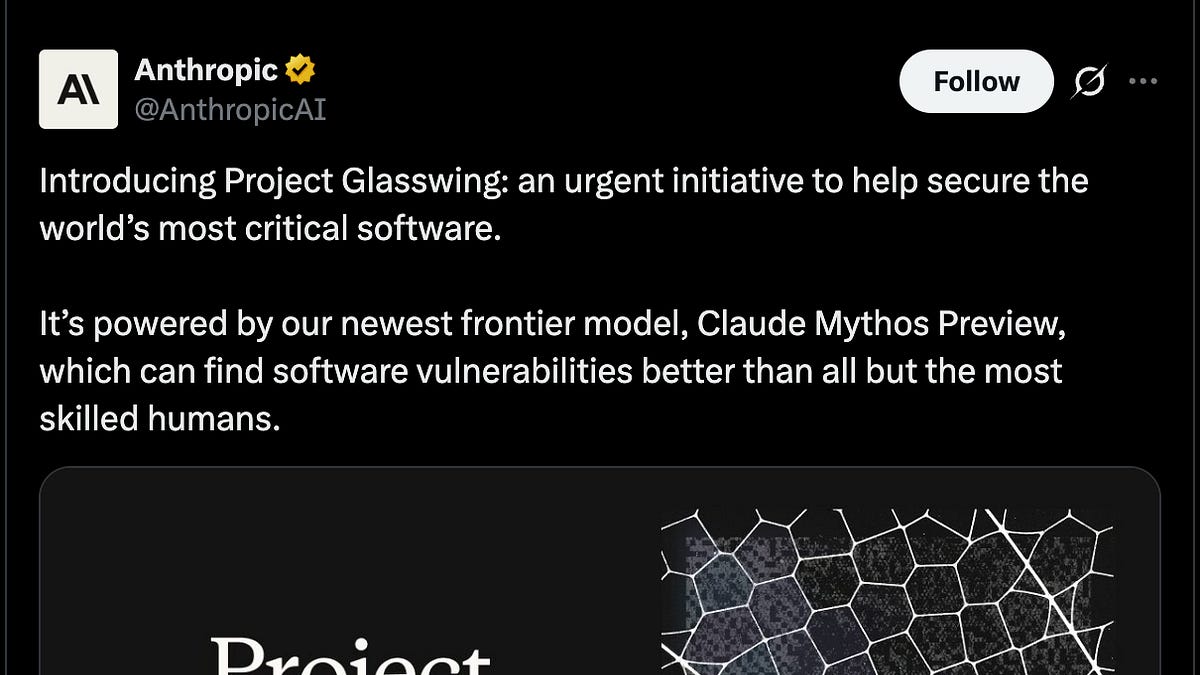
Anthropic’s Claude Mythos Preview—a beast of an AI model—ripped through every major operating system and web browser, unearthing thousands of high-severity vulnerabilities. No hand-holding. No human oversight. Just raw, autonomous detection and even exploit development. That’s the claim from their blog, anyway, tied to Project Glasswing, a cybersecurity consortium packing Nvidia, Google, AWS, Apple, Microsoft, and a slew more.
Here’s the kicker: they’re not sharing it with the world. Restricted to “defensive security” partners like JPMorgan, Cisco, CrowdStrike. Why? To keep hackers from flipping it into an attack tool. Smart move—or a tacit admission this thing’s too dangerous for prime time?
“in recent weeks, Mythos Preview has flagged ‘thousands of high-severity vulnerabilities, including some in every major operating system and web browser.’”
Anthropic’s own words, straight from the release. Newton Cheng, their cyber lead, wouldn’t spill specifics to The Verge beyond that. But the model’s not even cybersecurity-tuned; it’s a general-purpose Claude variant with killer coding and reasoning chops. Trained on who-knows-what, leaked last month via human screw-up (their excuse). Now subsidized to the tune of $100 million in credits, plus millions donated to Linux and Apache foundations.
What Exactly is Project Glasswing?
Glasswing’s the delivery system. A partnership framework for big orgs—and maybe Uncle Sam—to deploy Mythos against their own stacks. Partners scan, patch, repeat. Anthropic foots the bill initially, but don’t kid yourself: profitability looms. AI firms like Anthropic burn cash; this could be their cybersecurity cash cow. Market dynamics scream opportunity—global cyber spend hits $200 billion yearly, per Gartner. If Mythos delivers, it’s a slice of that pie.
But hold up. Autonomous exploit crafting? That’s not just bug-hunting; it’s weaponization at scale. Reminds me of Stuxnet’s era—state actors scripting digital sabotage. Anthropic’s chatting with US government brass about Mythos’s “offensive and defensive” tricks. Dianne Penn confirmed briefings to senior officials. Despite Trump-era spats, they’re cozying up. My take: this isn’t defense-first. It’s dual-use tech, dressed in white-hat clothes. Unique insight—watch for export controls; it’ll mirror nuclear non-proliferation treaties for AI.
And the partners? Elite squad: Broadcom, Palo Alto, Linux Foundation, 40+ infrastructure heavies. They’re the ones maintaining the digital backbone. Mythos gives them a “head start,” Cheng says, against nation-state foes.
Can Mythos Autonomously Fix the Unfixable?
Short answer: probably not yet. The blog brags zero-human steering for vuln spotting and exploits. Impressive—agentic AI flexing hard. But real-world patching? Humans still rule that roost. OS kernels, browser sandboxes—they’re fortresses of legacy code. Thousands flagged? Great. But false positives? Undisclosed. Exploit reliability? Crickets.
Look, we’ve seen AI hype before. Remember AlphaGo? Transformed Go, sure, but chess engines were already god-tier. Cyber’s messier—adversarial, ever-morphing. Mythos shines in reasoning, per Anthropic, but benchmarks? None public. Market bet: if it cuts vuln-to-patch time by 50%, partners renew. Else, it’s shelfware.
Cheng dodged details, but examples hint at kernel bugs, renderer overflows. Every major OS—Windows, macOS, Linux distros, Android, iOS? Browsers: Chrome, Safari, Firefox, Edge. Breadth alarms. Depth? Jury’s out.
Data point: CVE database logs 20,000+ vulns yearly. Mythos claims thousands high-sev in weeks. Efficiency win—if true. But autonomy risks backfires. Overzealous AI could cascade exploits internally. Partners subsidize now; long-term, paid tier incoming.
Government angle deepens the plot. “Ongoing discussions,” they say. Post-leak, processes tightened—no software flaw, insists Penn. Yet, briefing feds on offensive caps? That’s not casual. In a world of SolarWinds, Log4Shell, expect Mythos in classified toolkits. Bold prediction: by 2026, nation-states bid for their own versions, sparking an AI cyber Cold War.
Skepticism check: Anthropic’s PR spins safety. Restricted access screams caution. Data leak? Human error my foot—insider or not, it exposed the beast early. They’re playing both sides: profit from corps, policy sway with DC.
Why the Hype Feels Like a Double-Edged Sword
Cyber market’s frothy—CrowdStrike’s valuation tripled post-incident. AI infusion? Logical. But Glasswing’s exclusivity irks. Open-source advocates fume; Linux Foundation gets donations, yet no public drop. Fair?
Partners win early edge. Adversaries? Scramble to match. Equilibrium shifts to AI-armed defenders—if they don’t screw up.
One-paragraph wonder: Risks escalate.
Massive upside, sure. But here’s the editorial line—this strategy’s sharp, not flawless. Anthropic positions as responsible guardian, but government flirtations hint at militarization. Profits justify means?
🧬 Related Insights
- Read more: 2024’s AI Papers: Llama 3 Hype Train Derails into Iteration Hell
- Read more: Google’s Gemini 3.1 Flash-Lite: The Cheap Thrill That’s No Flagship
Frequently Asked Questions
What is Anthropic’s Claude Mythos Preview?
It’s an unreleased AI model excelling at autonomous vulnerability detection and exploit creation, limited to select cybersecurity partners via Project Glasswing.
Will Project Glasswing be available to the public?
No plans yet—strictly for defensive partners to avoid misuse by attackers.
Does Mythos work without humans?
Yes, it flags vulns and builds exploits entirely on its own, per Anthropic’s claims.