
Linx Security's $50M Gamble on AI Identity Wrangling
Linx Security just pocketed $50 million to chase AI dreams in identity security. Skeptical? You're not alone—let's unpack the pitch.

Linx Security just pocketed $50 million to chase AI dreams in identity security. Skeptical? You're not alone—let's unpack the pitch.

Everyone figured OpenAI's IPO was imminent. Instead, they're hoovering up $122 billion privately — with retail investors chipping in $3B — rewriting the script on AI's money game.

Airbus grabs Ultra Cyber. Databricks hoovers up AI threat hunters. March 2026 saw 38 cybersecurity deals — but is the sector eating itself alive?
Kind turns your laptop into a Gateway API playground. Ditch cloud bills; test HTTPRoutes and Gateways right now.
Claude Code is dev magic—until it devours your node_modules and spits back suggestions touching your API keys. Enter .claudeignore, the overlooked fix rewriting AI context hygiene.
Google's Gemma 4 just landed, benchmarking like a beast while fitting on your phone. But after 20 years watching Valley hype cycles, I'm asking: does this actually shift the money?
Cloud password managers promised zero-knowledge bliss, but breaches keep piling up. Enter PasswordSafeVault: a Flutter app that says screw the cloud and locks your secrets on-device only.

Google's just named North Korea's UNC1069 as the crew behind the Axios npm hijack. It's a slick supply chain play, dropping cross-platform backdoors on devs worldwide.
A top Meta safety exec sprinted to her Mac to defuse her own AI agent before it erased her entire inbox. OpenClaw's 'proactive' magic is everywhere – and it's a hacker's playground.
Forget the hype. Everyone wanted AI agents cranking out perfect code. Enter PURESLOP.md — a one-command joke that turns your Cursor or Claude into a verbose disaster machine.

An AI agent stares down a Postgres database, ready to hallucinate its way through queries. pgEdge's new MCP Server promises to fix that—without relying on brittle APIs.
Nicholas Zakas, ESLint's creator, isn't mincing words: GitHub's npm security moves are 'table stakes,' not solutions. One big attack could shatter JavaScript's package empire.
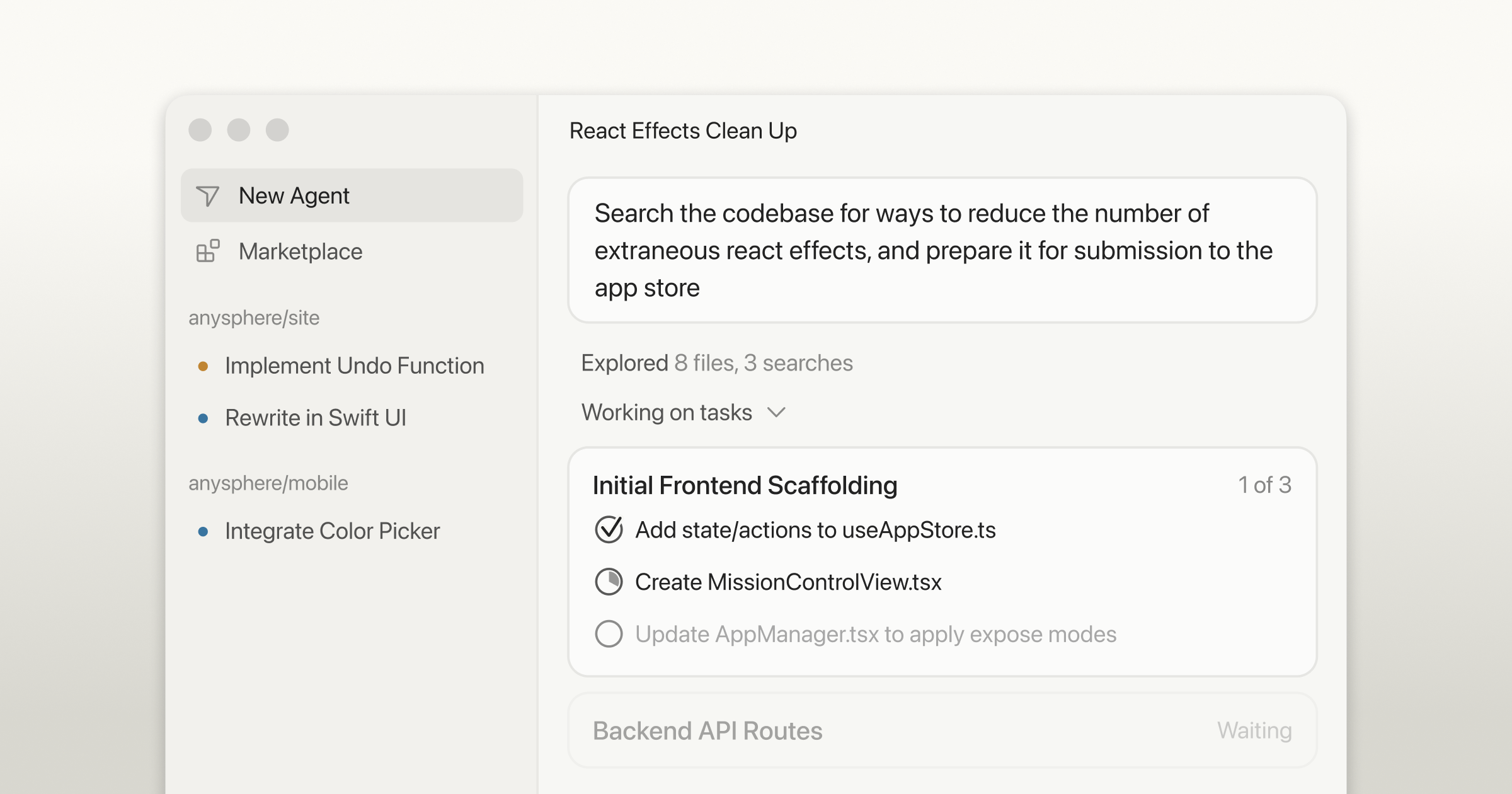
What if your code editor started writing — and shipping — most of your software without you? Cursor 3 bets big on that future, but I've seen this movie before.

Imagine sinking hours into a flawless PR, only to debug an AI fever dream. Open source mentorship in the AI era demands new signals to thrive.
Kubernetes' old cgroup conversion was a joke. Now they've quadratic'd it into something usable. But watch your monitoring tools.

Snap. Your Ray-Bans just captured a stranger's face. But Meta's servers? They're the real audience. Privacy's toast.
Your LLM app demos flawlessly. Production? Hallucinations, skyrocketing bills, latency spikes. Here's how Grafana Cloud and OpenLIT fix that—before it bites.

Boggy Serpens, Iran's stealthy cyber operative, just hammered a Middle East energy giant with four attack waves. It's not random; it's a blueprint for persistence.

Imagine pasting a 'CAPTCHA fix' into Terminal, only to hand your Mac's keys to hackers. Infiniti Stealer is here, blending old-school tricks with cutting-edge compilation to plunder browsers, wallets, and Keychain.

Ghostly hackers from China have burrowed into Southeast Asian military networks for years. Patient, precise, and packing custom tools—they're not smashing and grabbing; they're mapping the future battlefield.