Your next Slack file attachment might just hand your employer’s crown jewels to a hacker halfway across the world.
That’s the brutal reality for everyday developers — the ones grinding away in mid-sized firms or startups, not the Google elite with fancy internal tools. One slip, and you’re explaining to the boss why proprietary code ended up on a torrent site. Forget the tech details for a second; this hits real people where it hurts: jobs on the line, reputations shredded, maybe even lawsuits naming you.
Look, I’ve chased Silicon Valley hype for two decades. Watched companies promise the moon with “smoothly” sharing platforms (yeah, right), only to see breaches pile up. And here’s my unique take, one you won’t find in the original piece: this isn’t new — it’s the 2024 version of the 1990s floppy disk swaps that leaked Netscape’s browser secrets, kickstarting the open-source wars. History rhymes, folks; we’re just fancier now.
Why Do Developers Still Zip Code to External Drives?
Convenience. Pure, intoxicating convenience.
But.
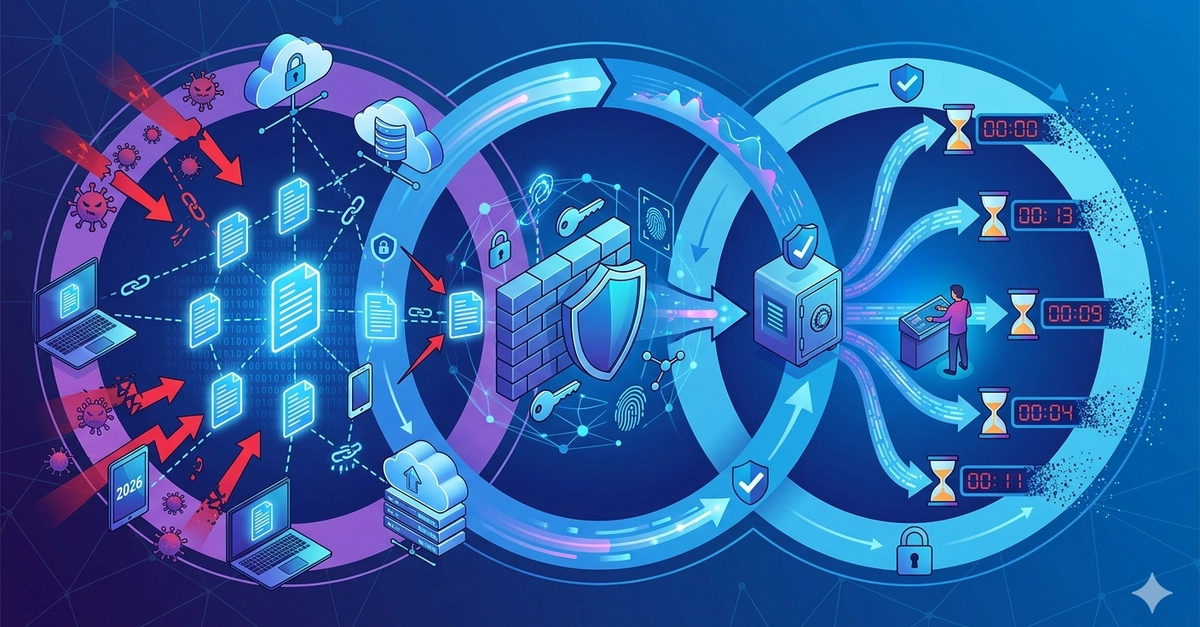
It’s a trap. External tools like Dropbox, Google Drive, or even personal email scream “easy,” yet they’re built for grandma’s vacation pics, not your company’s trade secrets. The original article nails it: “Public links are a ticking time bomb. Many services generate shareable links that are ‘public’ by default.”
Spot on. One wrong click — paste that link in the wrong channel, forget to set expiry — and bam, indexed by Google. I’ve seen it: a dev shares a config file with API keys (oops), and suddenly competitors are peeking. Who profits? Not you. The cloud giants rake in ad dollars from the chaos, while you’re updating your resume.
Compromised accounts? Laughable how often we ignore ‘em. Your buddy’s Gmail gets phished — poof, every shared snippet’s exposed. No corporate SSO, no zero-trust nonsense; just wide-open doors.
And compliance? Don’t get me started. GDPR fines hit millions; HIPAA breaches kill careers. Contracts? They’re landmines waiting for that “quick share.”
This isn’t paranoia — it’s pattern recognition after 20 years watching VCs fund the next “secure” tool, only for it to flop.
Is Your Team’s Source Code Bleeding Out via Chat Apps?
Short answer: probably.
Version drift alone should scare you straight. Email a module? Chat attachment? Now you’ve got five “latest” copies floating around, each with subtle bugs. “It works on my machine” becomes the team war cry. No audit trails in Slack or Drive — good luck proving who tweaked what when the prod outage hits.
Breaks CI/CD too. Modern dev’s all pipelines, Git flows, automated bliss. Sidestep that for a WeTransfer link? You’re injecting manual crap, silos, delays. The author whines about this frustration leading to SimpleDrop — their own tool (smells like promo, doesn’t it?). Fair enough, but ask: who’s monetizing your pain here?
Real cost? A breach ain’t cheap. Verizon’s DBIR pegs average at $4.5 million. For a startup? Lights out.
I’ve got a prediction: with AI scraping the web for training data, leaked code will fuel knockoff models. Your algos train the competition’s ChatGPT clone. Bold? Nah, inevitable.
Legal exposure piles on. IP theft lawsuits — remember Waymo vs. Uber? Started with a hard drive of secrets. Today, it’s a Drive link. Regulated fields? Kiss goodbye to clients if you flout rules.
The ‘Secure’ Alternatives That Aren’t Hype
Ditch consumer junk. Internal Git repos, enterprise Slack with E2E, or approved vaults like GitHub Enterprise.
But habits die hard — train your team. Checklists before sharing: approved? Access controls? Audit log? Legal ok?
The original pushes questions like that. Smart.
Build culture. Reward caution, not speed. Scales better than any tool.
Me? I’d audit shares weekly. Caught a schema leak once — indexed briefly, panic city. Lesson: act like it’s always public.
External tools tempt because they’re free(ish). But freedom’s got a price.
🧬 Related Insights
- Read more: Genetic Algorithms Aren’t Magic—Here’s Why They Actually Work (and When They Don’t)
- Read more: Archergate Ends License Lockouts for Good
Frequently Asked Questions
What are the biggest risks of sharing source code on Google Drive?
Data leakage from public links, no real access controls, and account hacks — your code ends up searchable or stolen.
How can developers safely share internal code snippets?
Use org-approved tools with E2E encryption, expiry links, and audit logs. Skip personal accounts entirely.
Does pasting code into Slack violate company compliance?
Often yes — lacks proper logging and security. Check your policies; it could breach GDPR or contracts.