IAM wrecked my OCI world.
Three words that haunted weeks of debugging hell. Picture this: you’re architecting a shiny Oracle Cloud Infrastructure lab—instances spinning up, networks humming like a well-oiled hive—but every launch attempt? Crickets. Or worse, cryptic errors that whisper ‘not authorized’ before vanishing.
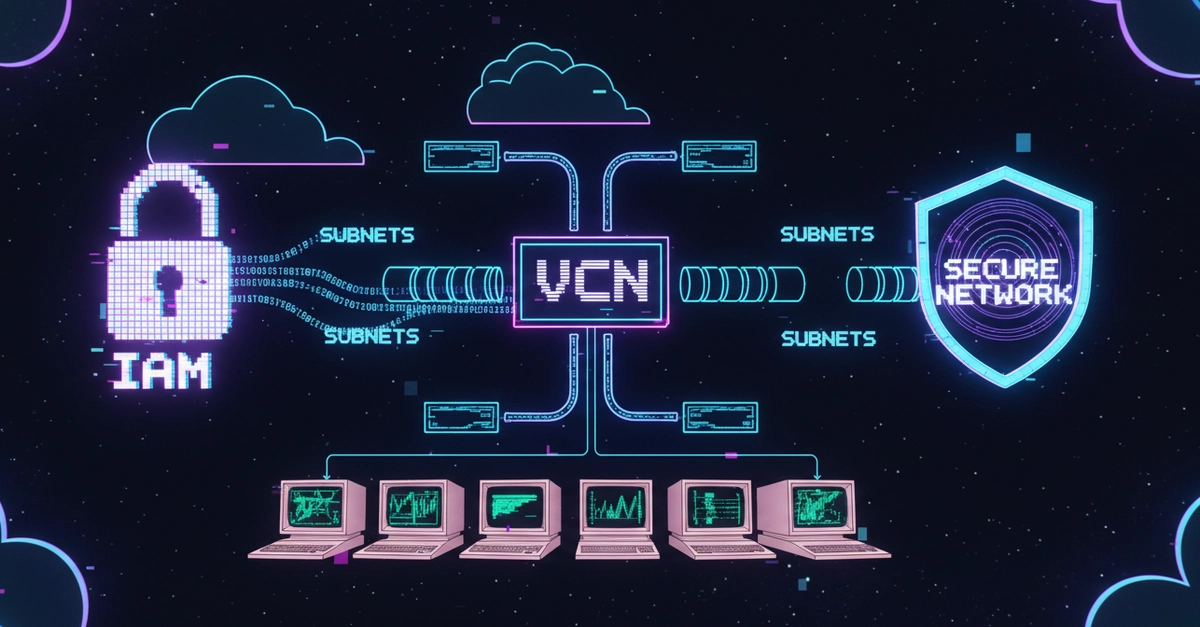
It wasn’t my code. (Swear on my keyboard.) I’d triple-checked scripts, poked at VCNs, even rebooted the console in desperation. But nope. The real culprit? Identity and Access Management. OCI’s IAM, that invisible bouncer at every cloud door.
Here’s the madness: IAM failures don’t scream. They nudge. Resources half-launch, APIs ghost you, and you’re left chasing shadows across compute, storage, block volumes. I bounced between tabs—networking one minute, shapes the next—like a frog on hot coals, losing context faster than a bad Zoom call drops.
Slowing down saved me. Finally, I dissected error logs, line by gruesome line. And there it was, glaring in the policy void: ‘Allow group to read instance-images in tenancy.’ Boom. Added that nugget, and poof—instances flew, everything clicked. No architecture overhaul. No Terraform rewrite. Just permissions.
Most cloud failures aren’t about what you built, they’re about what you forgot to allow.
That’s the raw truth from the trenches. Spot on.
Why Does OCI IAM Trip Up Even Pros?
Think of IAM as the feudal lord of your cloud kingdom. Groups, policies, compartments—it’s a hierarchy sharper than a samurai sword. Miss one verb (read, manage, use), and your empire crumbles. OCI amps this with dynamic groups and tag-based access, which sounds futuristic (it is), but bites if you’re not vigilant.
Newbies dive in assuming ‘tenancy admin’ covers all. Wrong. OCI’s least-privilege model—borrowed from the AWS gospel—forces granular policies. It’s like giving your kid the car keys but forgetting the gas money; they’ll strand halfway to school.
My unique twist? This echoes the 90s Unix wars. Remember chmod gone wrong, locking you out of your own box? OCI IAM is that on steroids—a multitenant maze where one forgotten scope cascades into lab Armageddon. But here’s my bold call: in the AI agent swarm coming (think autonomous DevOps bots provisioning fleets), IAM mastery won’t be optional. It’ll be the unbreakable moat separating scripted chaos from symphonies of scale.
And OCI’s PR spin? They tout ‘enterprise-grade security’—fair—but bury the IAM learning curve under shiny console tours. Callout: it’s not hype, just underlit. Labs break because docs assume you’re already enlightened.
Short para for punch: Fix IAM first. Always.
Now, the deep dive—how I traced it.
Error: ‘Authorization failed or requested resource not found.’ Classic red herring. Sounds like a bad ARN or missing compartment. But drill down: audit logs in OCI Console > Identity > Federation > Audit. Filter by failure. Boom—policy eval traces pinpoint the gap: instance-images read denied for your group in root tenancy.
Policy fix? Hop to Identity > Policies. New policy:
Allow group MyLabGroup to read instance-images in tenancy
That’s it. Attach to compartment or tenancy. Test with CLI: oci compute image list --compartment-id ocid1.compartment...
But wait—dynamic groups? If your instances self-register (common in IaC), add Allow dynamic-group MyDynGroup to ... too. And tags! OCI’s sweet spot: Allow group LabUsers to manage instance-family in compartment where all {request.principal.type = 'cloudshelluser', target.tag.namespace.lab = 'devlab'}. Vivid, right? Like tagging sheep in a cosmic pasture so only the right shepherd milks ‘em.
How Do You Bulletproof OCI IAM Forever?
Step one: compartment jailbreak. Nest ‘em like Russian dolls—lab in dev, prod in its vault. Assign groups per tier.
Step two: policy templates. OCI’s got ‘em under Stock Policies, but customize. Steal from Oracle’s GitHub repo—real gold.
Three: automate with OCI CLI or Terraform. My Terraform snippet post-fix:
resource "oci_identity_policy" "lab_policy" {
compartment_id = var.tenancy_ocid
description = "Lab IAM fix"
statements = ["Allow group MyLabGroup to read instance-images in tenancy"]
}
Deploy, done. No more manual drudgery.
Four—and this is the wonder: integrate with AI tools. Throw errors into GitHub Copilot or Claude; it’ll spit policy stubs. We’re entering an era where IAM debugging feels like chatting with a cloud whisperer.
Is OCI IAM Worse Than AWS or Azure?
Nah. All three clouds worship at the IAM altar. AWS IAM’s JSON hellscapes are wordier; Azure RBAC mixes roles like a drunk bartender. OCI? Cleaner syntax, but tenancy-scoped quirks catch you flat-footed. My prediction: as multi-cloud becomes norm (Kubernetes fleets spanning realms), universal IAM translators—AI-powered—will emerge. Five years max.
Real talk: that ‘randomly broken’ feel? It’s cognitive overload. Humans juggle 7±2 chunks (Miller’s law); cloud configs explode that. Solution? Observability kings like OCI Logging Analytics. Query failures, visualize policy gaps—it’s like X-rays for permissions.
One-sentence gut check: IAM isn’t sexy, but ignore it and your cloud dreams evaporate.
Extended ramble: I’ve seen teams burn millions on ‘architects’ who miss this, rebuilding from scratch. Don’t. Next time a resource 404s or 403s, skip compute/networking rabbit holes. IAM audit. 80% fix rate, easy bet.
Tie to future: AI platforms? They’ll provision OCI labs at warp speed—fine-tune Llama on custom images, orchestrate GPU fleets. But one IAM snag? Agent grinds to halt. Futurists like me see IAM as the neural gatekeeper of intelligent infra. Master it now.
If something feels randomly broken in the cloud, start with IAM first.
Preach.
🧬 Related Insights
- Read more: ShadCN UI in 2026: Copy-Paste Model That’s Eating Traditional Libraries Alive
- Read more: Ditching Claude’s LLM Roulette: Why Duckflux Delivers Deterministic AI Pipelines
Frequently Asked Questions
What causes IAM errors in OCI?
Silent permission gaps—like missing ‘read instance-images’—block resource access without obvious crashes. Check audit logs first.
How do I fix OCI lab permissions quickly?
Add targeted policies via console or Terraform: ‘Allow group YourGroup to read instance-images in tenancy’. Test with CLI.
Does OCI IAM differ from AWS IAM?
Yes—cleaner statements, tenancy focus, dynamic groups/tags. But same least-privilege pain; learn one, adapt fast.