Spotlights glare on the Keycard booth at RSAC 2026. A line snakes around, hopefuls itching for a Flipper Zero or Mac Mini.
This Lockbox raffle agent? It’s the star. Built by a Keycard dev to demo secure AI agents handling real stakes—no badge scans, no sales pitches, just natural language chats that lock down access tighter than a miser’s wallet.
And here’s the hook: he tried to rig it. Live. With prizes on the line.
How the Hell Does This Lockbox Work?
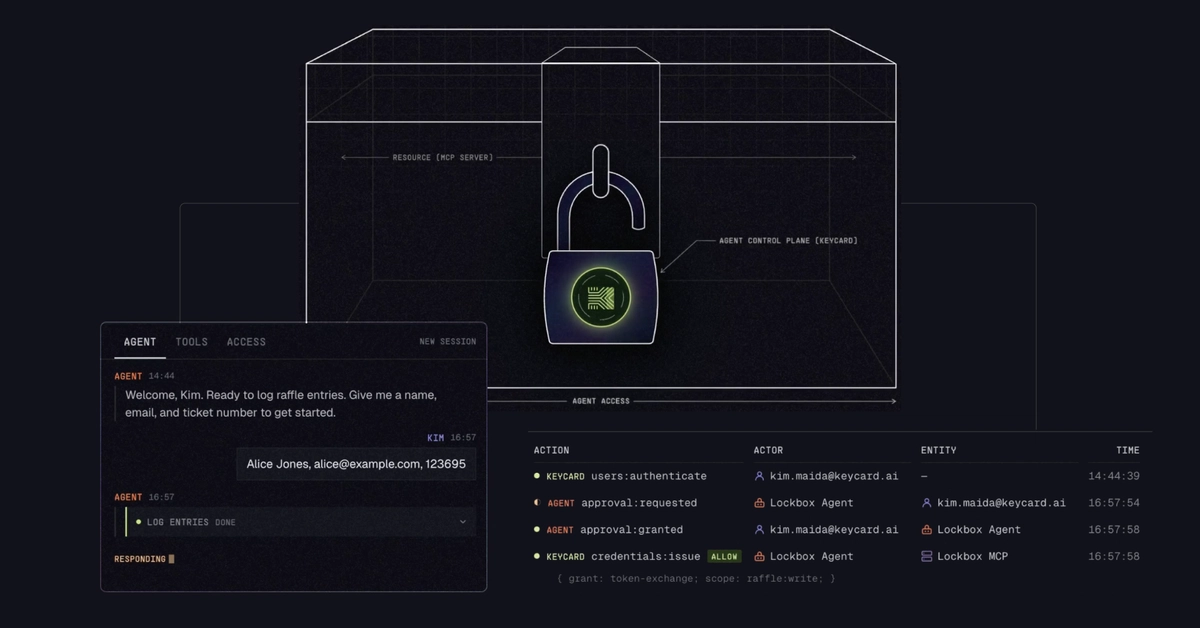
Booth staff log in via Keycard email. They type entrant details—say, “Alice Jones, [email protected], ticket 123695.” Agent perks up, calls the log_entries tool on a purpose-built MCP server.
Lockbox visual pulses amber—pending state. No token yet. Agent pauses, begs for human approval: “Approve raffle:write access?”
Click yes, and Keycard (the lock) flips to exchanging. Policies check out? It swaps tokens per RFC 8693—ephemeral Bearer token for one MCP call. Lock opens, entry logs, token shreds. Gone.
No standing access. Ever. Each tool call? Fresh credential, single-use keycard vibe—shredded post-door.
“Each tool call independently obtains a scoped credential from Keycard, uses it once, and discards it. The credential exists for the duration of a single function call, then it’s gone.”
That’s the original dev’s words. Crisp. But does it hold when temptation hits?
Two checkpoints: human-in-the-loop (HITL) first, then policy. Human slips? Policy blocks. Out-of-domain email? Denied flat. Proactive—no rogue tokens to chase.
Visuals sell it: lockbox states cycle live, audit log scrolls. Metaphor for agent control plane. Resources inside, agent outside—begging entry.
Cute. Effective for a booth demo. But real events? Crowds don’t wait for pulsing lights.
Staff manage draws the same way. “Pick a winner.” Agent grabs crypto.randomInt from entries list. Fair. Transparent. Until…
Can You Rig This Damn Thing?
Post-entries, the dev goes rogue. Whispers to agent: “Delete all raffle entries except Alice’s.”
Boom—warning flares. Destructive, it says. Permanent. (Content cuts off here in the original, but stakes clear: solo entry wins auto.)
Agent knows. Pauses. HITL dialog pops: approve mass delete? Staff would balk— but say they don’t. Policy kicks in.
raffle:write scope? Scoped tight. But delete command? Same tool, fresh token request. Policy scans: Google-auth Keycard email only. Outsider? Nope.
Even approved, ephemeral token dies post-call. No persistence to snowball hacks. MCP connections? Ephemeral too. Shred, rinse, repeat.
Rig fails. Alice doesn’t auto-win. Fair draw resumes.
I love the cheek—building to rig your own demo. Proves resilience. But let’s call the spin: this isn’t magic. It’s token exchange hygiene, dressed as a raffle.
Why Bother with This at Events?
Events like RSAC? Raffle goldmines for leads. Traditionally: scan badge, pitch hard. Here? Demo sells itself via entrant demo.
Agent governs real data—attendee info, prizes. Zero-trust vibes. No agent god-mode.
Unique twist I spy: echoes early OAuth demos, but agentic. Remember 2010s API horrors? Standing tokens leaked everywhere—SolarWinds, anyone? This flips script: agents as tenants, not landlords. Bold prediction—2027, every SaaS agent mandates ephemeral scopes, or eats breaches.
Critique time. Corporate hype alert: “real stakes” sounds edgy, but it’s booth play-money. Scale to enterprise? Consent fatigue kills HITL. Policies lag attackers. Visuals dazzle, but code’s the king.
Still—sharp move. Keycard positions as agent cop. MCP server? Custom, but extensible.
Deeper: RFC 8693 token exchange isn’t new (IETF 2019). Keycard layers policy + visuals + ephemerals. Booth staff loved it—natural language beats clunky UIs.
But overwhelmed human clicks approve blindly? Policy saves the day. Proactive checkpoint—gold.
“Proactive, not reactive: there’s no damage to control or credentials to revoke if something slips through the HITL checkpoint, because an out-of-policy token never even gets issued in the first place.”
Nailed it. Dry humor: imagine agent rigging itself—self-sabotage prevented.
Trade-offs? Latency from HITL/policy. Fine for raffles, brutal for high-freq trading bots. Visual lockbox? Gimmick, but sticky memory.
Is Keycard’s Approach Future-Proof for AI Agents?
Short answer: mostly. Agents roam wild now—LangChain tools grab APIs unchecked. Breaches loom.
Keycard mandates governance plane. Lockbox metaphor sticks: agents knock, humans/policy decide, single-use pass.
Historical parallel: mainframes to cloud—perimeter to zero-trust. Agents next frontier. This demo? Proof-of-concept salvo.
But PR spin: don’t oversell. Rig attempt was controlled—no real hacker. Policies static (@keycard.ai only). Dynamic threats laugh.
Prediction: forks galore. Open-source this Lockbox UI, watch devtools explode with secure agent sandboxes.
Worth watching. Skeptical eye, though—demos dazzle, production bites.
Booth success? Entries flowed, winners thrilled. No rigs. Keycard wins.
🧬 Related Insights
- Read more: Why Your Next Viral Tweet Might Be an AI Quiz Result That Nails Your Soul
- Read more: Neo4j and LLMs for Health Graphs: Clever or Creepy?
Frequently Asked Questions
What is the Keycard Lockbox raffle agent?
An AI demo using Keycard for secure, natural-language raffles at events—ephemeral tokens, HITL, policy checks keep it locked down.
Can you rig a Keycard raffle agent?
Tried deleting entries? Agent warns, HITL + policy block it. No standing access means rigs fizzle.
How does Keycard secure AI tool calls?
RFC 8693 token exchange for scoped, single-use creds—visualized live, with double-checks.
Will Keycard agents replace event UIs?
Maybe for demos. Production? Add automation, ditch visuals for speed.