What if that innocent-looking Google link in your inbox is a one-way ticket to scam city?
Redirects in phishing. They’re everywhere in 2026 – or at least in 21% of the phishing emails sniffed out this year. Jan Kopriva’s fresh dig into spam traps and filters paints a picture that’s equal parts alarming and absurd. Attackers probing for open redirects on your domains? Check. Half-baked Google tricks? Double check. And us? Still shrugging it off as low-risk fluff.
Here’s the kicker from his analysis:
Redirect-based phishing accounted for a little over 21 % of all analyzed messages sent out over the first 3 months of 2026 – specifically for 32 % in January, 18 % in February and 16.5 % in March.
Over 350 emails, not a huge sample, but enough to make you spit out your coffee. January hit 32%. That’s no fluke.
Why Dismiss Open Redirects as Harmless?
They’re not OWASP Top 10 material anymore. Fine. But attackers treat them like gold. Why? Simple: a link to google.com screams ‘safe’ to your overworked brain – and to basic email scanners. Click. Redirect. Boom, phishing page. No red flags waving.
Look at the probes Kopriva sees: /out.php?link=https://domain.tld/. Every month. Persistent little bastards.
And it’s not just wild-west open redirects. Half-open ones on Google, Bing – tokens that last forever, reusable anywhere. Lazy design? Or just begging for abuse?
One para. Punch.
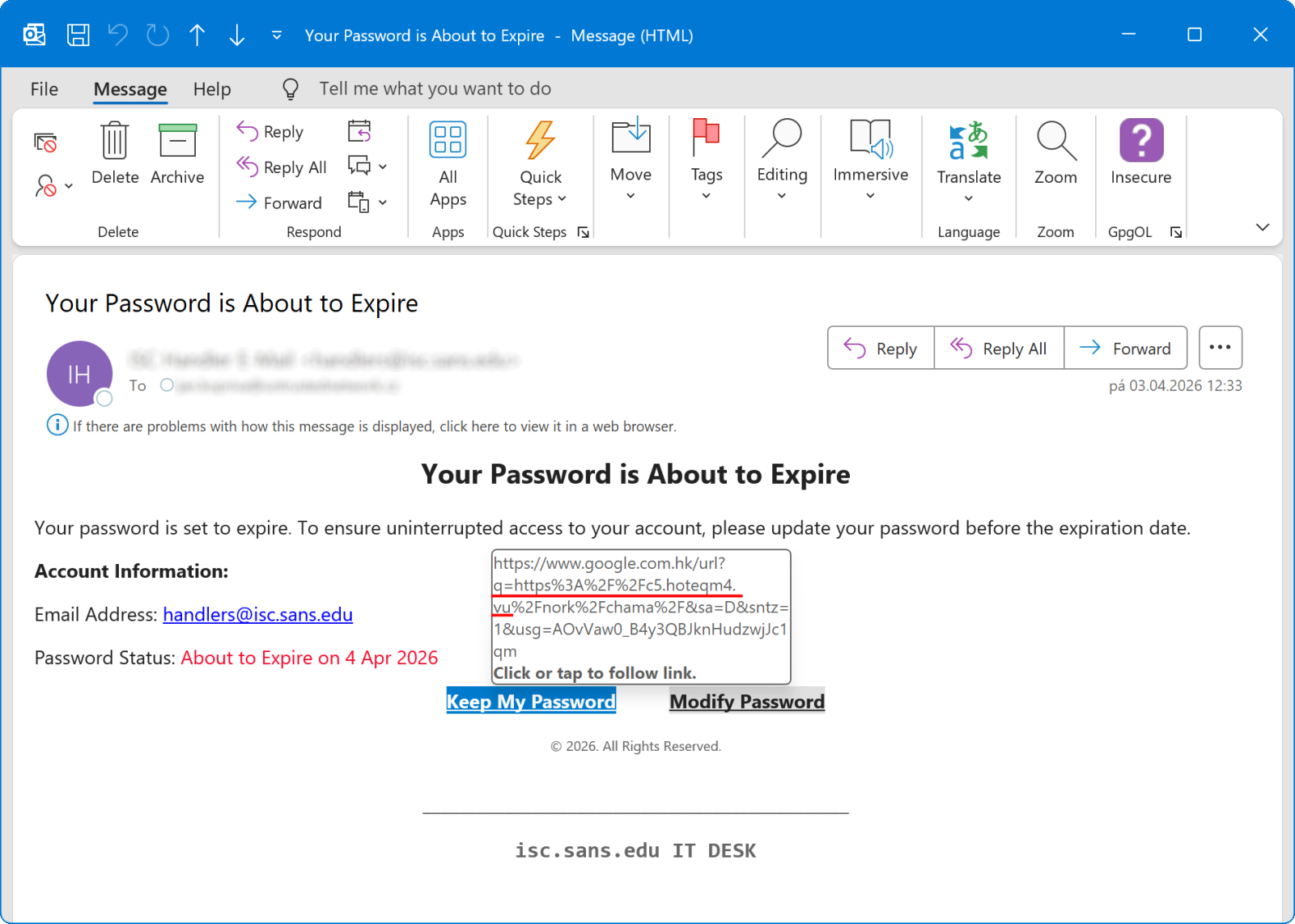
Threat actors don’t care about your risk ratings. They exploit what’s there. Kopriva’s seen campaigns abusing Google’s ‘logout’ redirects – legitimate-looking URLs that flip to malware mid-flight. Images in his post show the chain: email link to Google, token magic, fake login. Elegant. Evil.
But here’s my twist, the one Kopriva skips: this reeks of 2010 MySpace phishing glory days. Remember those? Profile scrapers hid behind redirects too. History rhymes – we patched MySpace, ignored the lesson, now Big Tech’s toys get the same treatment. Prediction? If devs keep half-assing context checks, redirects hit 30% by year’s end. Bet on it.
How Bad Is Redirect Abuse in 2026 Phishing?
Kopriva’s Q1 tally: 21% overall. Drops each month, sure – maybe scanners catching up. Or attackers pivoting. Doesn’t matter. URL shorteners count too, though rare. Tracking pixels, ad redirects, logout traps – variety pack of doom.
Not all classic opens. Many ‘half-open’ – need a token, but who verifies lifetime or IP? Nobody. Reused in blasts. Google-style reigns, but Bing joins the party.
Short para. Breathe.
And the irony? We call it a ‘nuisance.’ While blackhats scan your site monthly. Traffic logs don’t lie. Ignore at your peril.
Phishing thrives on trust. Legit domains cloak the poison. Filters choke on that. Users? Click happy. Result: credentials harvested, ransomware queued.
Kopriva’s polite: monitor, restrict. Me? Torch those endpoints. No mercy. If you need redirects, tie ‘em down – session-only, IP-bound, abuse alerts screaming.
Attackers’ Favorite Redirect Playground
Google leads, naturally. That ‘half-open’ gem from last year? Still kicking. Tokens eternal, context-free. Perfect for mass phishing.
Others: ad networks, trackers. Even your logout page – genius misuse. Log out? Nah, log into my fake bank.
Probes constant. Kopriva’s domains buzz with them. Yours too, probably. Check your logs. Today.
Unique angle: corporate PR spin calls this ‘low impact.’ Bull. It’s the gateway drug to OAuth hell, as Johannes noted. Chains to real breaches. Wake up.
Dry laugh: we’re fixing quantum bugs while redirects pick our pockets.
What Now? Stop the Madness
Dev teams: audit yesterday. Kill open ends. Log abuse. Block by default.
Users: hover links. Google? Really? Pause.
Filters: evolve. Signature alone? Dead.
Kopriva’s right – don’t ignore. But let’s not whisper. Scream it.
Long para time: in a world drowning in AI threats, these old-school tricks persist because they’re simple, effective, and overlooked; attackers scan tirelessly, we patch sporadically, phishing volumes explode quarterly, yet redirects hold steady at one-in-five, a reminder that security’s not about shiny new vulns but the dusty ones we forgot, the ones that blend legitimacy with lies so smoothly your aunt clicks without blinking, landing creds in dark web shops before dinner’s cold.
FAQ incoming.
🧬 Related Insights
- Read more: FBI Tallies $17.7 Billion Cyber Fraud Haul: Crypto Kings, AI Deepfakes, and Your Wallet’s Nightmare
- Read more: Microsoft’s February 2026 Patch Tuesday Plugs Six Actively Exploited Zero-Days
Frequently Asked Questions
How common are redirects in phishing emails 2026?
About 21% in Q1, per analyzed samples. January peaked at 32%.
Are open redirects still a real threat?
Damn right. Attackers probe constantly; they bypass filters via legit domains.
How to stop open redirect phishing?
Audit endpoints, restrict with context checks, monitor abuse logs.