Imagine you’re a teacher in Kyiv, buried in emails. One pops up from ‘CERT-UA’ — urgent warning about threats. You click. Boom. Remote hackers now puppeteering your PC. That’s the nightmare these clowns tried to unleash on a million Ukrainians.
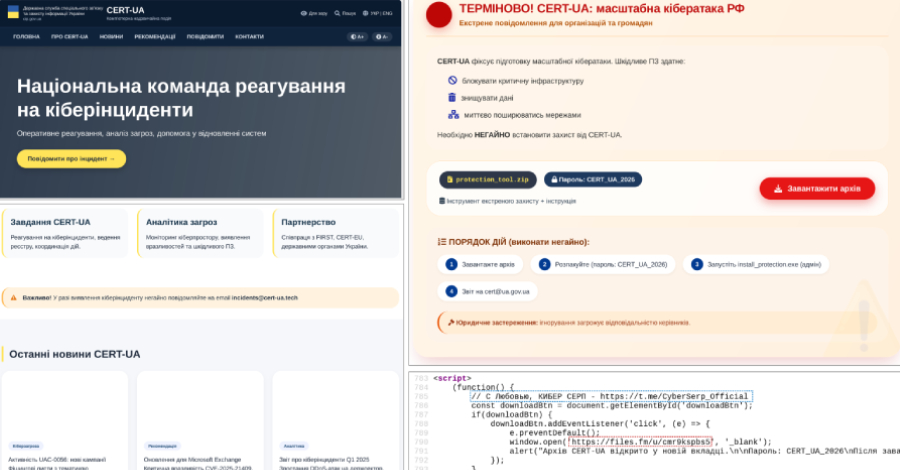
CERT-UA impersonation campaign. That’s the poison here. Not some abstract cyber skirmish — real folks in schools, hospitals, banks, clicking in panic.
And it barely worked. Few infections. Mostly ed workers’ home rigs. CERT-UA swooped in, cleaned house. But the gall? Impersonating Ukraine’s own shield while Russia-linked goons (probably) lob this garbage.
Look, this reeks of desperation. UAC-0255, the tracked crew, fired off emails March 26-27, 2026. Password-zipped file from Files.fm. ‘Install our protection tool,’ it lied. Targets: state orgs, docs, sec firms, schools, finance, devs.
Emails from incidents@cert-ua[.]tech. Fake site AI-spun — HTML screams it, with a lovesick note: “С Любовью, КИБЕР СЕРП.” Cyber Serp’s calling card.
Why Pretend to Be CERT-UA?
Simple. Trust. In war-torn Ukraine, CERT-UA’s the good guys — the ones yelling ‘duck’ when missiles fly digital. Pose as them? Panic clicks skyrocket. It’s psychological judo.
But here’s my take — a twist the reports miss: this echoes the 2017 NotPetya farce. Russian ops then hid in Ukrainian accounting software, nuked the world by accident. Boasted big, delivered chaos. Today? Cyber Serp’s channeling that same amateur swagger, but with AI crutches. Prediction: expect floods of these sloppy, bot-built phish. Cheap, endless, zero skill barrier. Ukraine’s inboxes? Target practice.
Cyber Serp’s Telegram — birthed November 2025, 700+ subs — brags a million ukr[.]net blasts, 200k infections. Lies, mostly. CERT-UA calls it a dud.
“No more than a few infected personal devices belonging to employees of educational institutions of various forms of ownership were identified,” the agency said. “The team’s specialists provided the necessary methodological and practical assistance.”
That’s the real quote. Dry, Ukrainian efficiency. Serp’s bloviation? Pure cope.
They claim: “We are not bandits – the average Ukrainian citizen will never suffer.” Sure, pal. Just snag teacher laptops for ‘ops.’ Noble.
And last month? They crowed about hacking Cipher, Ukraine’s sec firm. Full server dump, client DB, CIPS code. Cipher shrugs: one rogue creds, no biggie, one project, zilch sensitive.
PR spin? Cipher’s playing cool. Smart. But reeks of underplayed breach.
What’s AGEWHEEZE Pack?
Go-lang RAT. WebSockets to 54.36.237[.]92. Commands galore: shell exec, file fiddles, clipboard grabs, mouse/keyboard ghosts, screenshots, process/service wrangling.
Persistence? Scheduled tasks, registry hacks, startup folder squat. Nasty if it sticks.
But flop city. Why? Ukrainians wise up fast — war hones that. Plus, Files.fm? Sketchy as hell. Who bites?
Serp’s crew — self-styled ‘cyber-underground from Ukraine.’ Laughable. Tracks Russian. UAC-0255’s playbook screams it.
Dry humor time: they’re ‘from Ukraine’ like Putin’s a pacifist. Telegram tough guys, AI site builder (lazy), million-send brag with handful hits. Peak cyberpunk fail.
Does This Escalate Ukraine’s Cyber Hell?
Short answer: not yet. But patterns worry.
War’s third year — cyber’s the cheap front. Impersonate defenders? Bold escalation in info ops. If they refine — ditch AI slop, tighten phish — next wave bites harder.
Unique angle: remember Fancy Bear’s 2016 DNC spear? Same trust game, bigger stage. Here, localized, but scalable. With AI, nation-states (or proxies) spam variants daily. Ukraine’s a lab rat; lessons export global.
Real people hit? Teachers now paranoid-check every email. Hospitals double-scan zips. Fatigue sets in — that’s the win for attackers.
Corporate hype? Cyber Serp’s. ‘200k owned!’ Nope. CERT-UA debunks. Media laps boasts; we shouldn’t.
Skepticism’s our job. This ‘campaign’? More meme than menace. Yet vigilance — non-negotiable.
Lessons Before You Click
Don’t. Ever.
Zip from strangers? Trash. CERT-UA comms? Verify domains — cert.org.ua, not .tech crap.
Tools: MFA everywhere. Email filters on steroids. Train staff — war’s made Ukraine pros; rest of us? Catch up.
Bold call: this flops, but signals AI-phish boom. 2027? Billions targeted, sloppier nets wider.
Stay sharp. Or become the screenshot.
🧬 Related Insights
- Read more: Pixel 9 Cracked Open: BigWave Driver’s Triple Bug Sandbox Escape
- Read more: AI Code Boom Overwhelms AppSec — Black Duck CEO Sounds Alarm
Frequently Asked Questions
What is AGEWHEEZE malware?
Go-based RAT for remote control — commands, files, keylogs, screenshots. Ties to Russian-tracked UAC-0255.
How did hackers impersonate CERT-UA?
Fake emails from cert-ua[.]tech, AI-built site, ZIP ‘tool’ pushing the RAT. Blasted 1M ukr.net boxes.
Is Cyber Serp really Ukrainian?
They claim it. Evidence says Russian proxy — tactics, targets, bluster match GRU style.